How to Perform a Self-Assessment for RED Cybersecurity Compliance
The EU Radio Equipment Directive requires cybersecurity compliance under EN 18031 for internet-connected devices. This guide explains how manufacturers can perform a self-assessment (Module A) - from scoping the applicable standards and identifying assets to completing decision trees, running test plans, and generating the Declaration of Conformity.
March 25, 2026
Key Takeaways

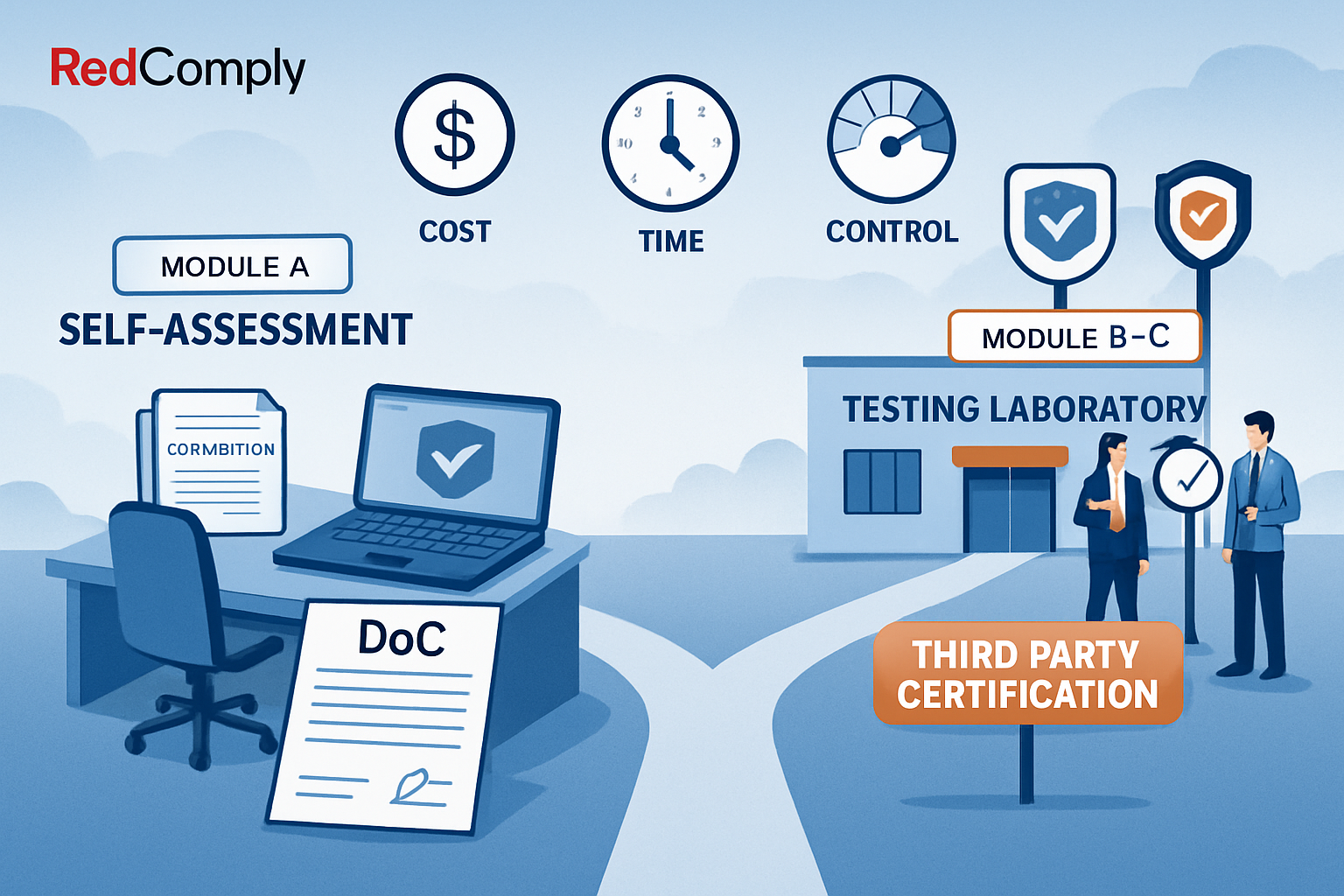
A self-assessment for RED cybersecurity compliance is the process by which a manufacturer independently evaluates and documents that their radio equipment meets the cybersecurity requirements of EN 18031, without involving a third-party notified body. Known formally as Module A (internal production control) under the EU conformity assessment framework, this path puts the manufacturer in full control of the assessment - and in full responsibility for the result.
Self-assessment is legally valid: Module A conformity assessment is explicitly permitted under the Radio Equipment Directive (RED) for cybersecurity requirements activated by Delegated Regulation (EU) 2022/30.
EN 18031 is the harmonised standard: Following EN 18031-1, EN 18031-2, and EN 18031-3 provides a presumption of conformity to RED Articles 3.3(d), 3.3(e), and 3.3(f) respectively.
The process is structured, not freeform: Self-assessment follows a defined workflow - scope definition, asset identification, section-by-section evaluation using decision trees, test plan execution, and Declaration of Conformity (DoC) generation.
Technical documentation is the deliverable: The entire self-assessment must be recorded in structured technical documentation that market surveillance authorities can review at any time.
Tools exist to accelerate the process: Platforms like RedComply automate the most time-consuming parts - table population, decision tree navigation, test plan calculations, and DoC generation.
What Is Module A and Why Does It Matter?

Under the Radio Equipment Directive (RED) - specifically Delegated Regulation (EU) 2022/30 activating Articles 3.3(d), 3.3(e), and 3.3(f) - manufacturers of internet-connected radio equipment must demonstrate cybersecurity compliance before placing products on the EU market.
The RED allows two conformity assessment routes:
Module A (Internal Production Control): The manufacturer performs the assessment internally, prepares the technical documentation, and signs the Declaration of Conformity themselves.
Module B + C (EU Type Examination + Conformity to Type): A notified body examines the product design (Module B) and the manufacturer confirms ongoing production conformity (Module C).
Module A is the self-assessment path. It means no external testing laboratory is required for the cybersecurity portion of RED compliance. The manufacturer takes full responsibility for evaluating the product against EN 18031 and documenting the results.
This matters because it gives manufacturers direct control over timelines, costs, and iteration speed. However, it also means the technical documentation must be thorough enough to withstand scrutiny from EU market surveillance authorities, who can request it at any time after the product is placed on the market.
When is Module A appropriate?
Module A is appropriate for most manufacturers who have internal cybersecurity expertise or access to compliance tooling. It is particularly suitable when:
Your engineering team understands the device's security architecture
You have access to EN 18031 and can map requirements to your product
You need to iterate quickly (self-assessment avoids the notified body queue)
You have a compliance platform or structured workflow to ensure completeness
If your team lacks cybersecurity expertise or the product has an unusually complex security architecture, Module B + C with a notified body may provide additional assurance - but it is not legally required.
Step-by-Step: The Self-Assessment Workflow

A complete RED cybersecurity self-assessment follows a structured sequence. Each step builds on the previous one, and skipping steps creates gaps that market surveillance authorities will identify.
The self-assessment follows a structured risk assessment process. Our risk assessment guide provides a detailed walkthrough of each phase.
Step 1: Define your compliance scope
Determine which parts of EN 18031 apply to your device based on its functionality:
EN 18031-1 (Article 3.3(d)): Network security - applies to devices that connect to the internet or a network
EN 18031-2 (Article 3.3(e)): Privacy and data protection - applies to devices that process personal data
EN 18031-3 (Article 3.3(f)): Fraud prevention - applies to devices involved in financial transactions or virtual currency
Most internet-connected devices require at least EN 18031-1. Many also require EN 18031-2. The scope determines which sections, tables, and requirements appear in your assessment.
Step 2: Identify and catalogue your assets
Before evaluating any requirement, you must identify what needs protection on your device. EN 18031 defines specific asset categories:
Security functions: Device features that implement security measures (authentication, encryption, access control, firmware verification)
Security parameters: Data that governs how security functions behave - split into Confidential Security Parameters (CSPs) and Sensitive Security Parameters (SSPs)
Network assets: Network resources, services, and interfaces exposed by the device
Privacy assets: Personal data processed, stored, or transmitted by the device (EN 18031-2)
Financial assets: Financial data or virtual currency handled by the device (EN 18031-3)
Asset identification is not optional. It is the foundation that every subsequent requirement evaluation depends on. If your asset inventory is incomplete, your assessment will have structural gaps.
Step 3: Work through compliance sections
EN 18031 organises requirements into compliance sections. Each section contains structured tables where you document how your device meets specific requirements. Key sections include:
Equipment Identification (device and radio module identification)
Access Control Mechanisms (authentication, authorization, default credentials)
Vulnerability Handling (disclosure, patching, monitoring)
Cryptography (algorithms, key management, certificate handling)
Software Update Mechanisms (secure update delivery and verification)
Logging and Monitoring (security event recording)
Network Monitoring (traffic analysis, anomaly detection)
Each table row requires specific information: what mechanism exists, how it works, which assets it protects, and what evidence supports the claim.
Step 4: Complete decision trees
Many EN 18031 requirements are evaluated through decision trees - structured sequences of yes/no questions that lead to a deterministic outcome: PASS, FAIL, or NOT_ASSESSED. Decision trees ensure that every requirement is evaluated consistently and that the rationale for each outcome is recorded.
For example, a decision tree for an access control requirement might ask: Does the device enforce authentication? If yes, does it use unique credentials? If yes, are default credentials changeable? Each answer leads to the next question or a final verdict.
Step 5: Execute the test plan
EN 18031 requires a three-tier test plan to validate your assessment:
Conceptual Assessment: Evaluates each test item against decision tree results and expert justifications - did the claimed security mechanism actually produce a passing outcome?
Functional Sufficiency Assessment: Tests whether the implemented security measures are sufficient for each assessment unit - are your controls adequate, not just present?
Functional Completeness Assessment: Identifies gaps - are there requirements that lack documented test items entirely?
Verdict conditions are evaluated automatically when using structured tools: patterns like "At least one PASS in column DT result" or "No FAIL entries present" determine whether each test item passes. The final verdict for each section is computed from pass/fail criteria masks.
Step 6: Generate the Declaration of Conformity
The Declaration of Conformity (DoC) is the final regulatory document. It compiles all assessment results into a structured PDF that demonstrates your device meets the applicable EN 18031 requirements. The DoC must include equipment identification (rendered as key-value pairs), assessment tables (rendered horizontally), decision tree outcomes, and test plan results.
Once signed by the manufacturer, the DoC enables CE marking and EU market placement.
Self-Assessment vs. Third-Party Certification
Choosing between Module A (self-assessment) and Module B + C (third-party) is one of the first decisions manufacturers face. Here is a direct comparison:
| Aspect | Module A (Self-Assessment) | Module B + C (Third-Party) |
|---|---|---|
Who performs the assessment? | The manufacturer internally | A notified body examines the design; manufacturer confirms production conformity |
Legal validity | Fully valid under RED | Fully valid under RED |
Cost | Lower (internal resources + tooling) | Higher (notified body fees + internal preparation) |
Timeline | Manufacturer-controlled | Dependent on notified body availability and review cycles |
Documentation burden | Full technical documentation prepared by manufacturer | Same documentation required, plus notified body review artifacts |
Iteration speed | Fast - changes can be re-assessed immediately | Slow - significant changes may require re-examination |
Market surveillance risk | Documentation must withstand authority review post-market | Notified body certificate provides additional assurance |
Best for | Teams with cybersecurity expertise or compliance tooling | Complex products or manufacturers without internal security expertise |
The key insight: the documentation requirements are identical regardless of which module you choose. Module A does not mean less work - it means you do the same work without paying a notified body to review it. The quality of your technical documentation is what matters.
Self-Assessment Readiness Checklist
Before starting your EN 18031 self-assessment, verify that your team and resources are ready. Use this checklist to identify gaps before they become blockers:
EN 18031 access: You have copies of EN 18031-1, EN 18031-2, and/or EN 18031-3 (whichever parts apply to your device)
Device security architecture documented: Your engineering team can describe all security functions, cryptographic implementations, network interfaces, and data flows
Asset inventory started: You have begun identifying security functions, security parameters (CSPs and SSPs), network services, and (if applicable) privacy and financial assets
Compliance tooling in place: You have a platform or structured workflow for completing compliance tables, decision trees, and test plans - not just spreadsheets
Internal expertise available: At least one team member understands cybersecurity concepts, EN 18031 structure, and the decision tree methodology
Test evidence available: You can provide evidence for each claimed security mechanism - configuration files, test results, code references, or architecture diagrams
DoC generation capability: You have a way to compile all assessment data into a structured Declaration of Conformity PDF
Management commitment: Leadership understands that the manufacturer bears full legal responsibility for Module A self-assessment
If three or more items are missing, consider either engaging a consultant for the initial assessment or using a dedicated compliance platform like RedComply that provides the structure and guidance to work through the process systematically.
Having the right tools makes a significant difference. See our comparison of EN 18031 clause mapping tools to evaluate your options.
Frequently Asked Questions
Is self-assessment really accepted for RED cybersecurity compliance?
Yes. Module A (internal production control) is explicitly permitted under the Radio Equipment Directive for the cybersecurity requirements activated by Delegated Regulation (EU) 2022/30. There is no legal requirement to use a notified body for Articles 3.3(d), 3.3(e), or 3.3(f). The manufacturer can perform the assessment, prepare the documentation, and sign the Declaration of Conformity independently.
How long does an EN 18031 self-assessment typically take?
The timeline depends heavily on device complexity and team readiness. For a moderately complex IoT device with one EN 18031 part applicable, a well-prepared team with proper tooling can complete the assessment in 2-4 weeks. Without structured tooling, the same assessment often takes 2-4 months due to the volume of tables, decision trees, and cross-references involved. Multi-standard assessments (EN 18031-1 + EN 18031-2 + EN 18031-3) take proportionally longer.
What happens if market surveillance finds problems with my self-assessment?
Market surveillance authorities can request your technical documentation at any time after market placement. If they find the documentation incomplete, inconsistent, or insufficient, they can require corrective action, restrict or withdraw the product from the market, and impose penalties. This is why thorough documentation is essential - not just checking boxes, but providing substantive evidence for every claim.
Can I switch from self-assessment to third-party certification later?
Yes. The conformity assessment module is chosen per product and can be changed for subsequent product versions or variants. Some manufacturers start with Module A for initial market entry and later engage a notified body (Module B + C) for additional assurance on high-volume products. The technical documentation you prepare for Module A is largely reusable for Module B + C.
Do I need to self-assess against all three parts of EN 18031?
No. Which parts apply depends on your device's functionality. EN 18031-1 (network security) applies to most internet-connected devices. EN 18031-2 (privacy) applies if the device processes personal data. EN 18031-3 (fraud prevention) applies if the device handles financial transactions or virtual currency. A simple Wi-Fi sensor might only need EN 18031-1, while a smart payment terminal would need all three parts.
Getting Started with RedComply
RedComply is purpose-built for EN 18031 self-assessment. The platform transforms the complex, document-heavy process described in this guide into a guided, structured workflow with AI assistance at every step.
Here is how RedComply supports each phase of your self-assessment:
Scope definition: Create a project, select which EN 18031 parts apply, and the platform automatically filters sections, tables, and requirements to show only what is relevant
Asset identification: Structured tables for documenting security functions, security parameters, network assets, privacy assets, and financial assets - with AI assistance to suggest and cross-reference entries
Section-by-section evaluation: AG Grid-powered compliance tables with decision tree integration, auto-populated fields, and real-time consistency checks
Test plan execution: Three-tier test plan with auto-calculated verdict conditions - the platform detects patterns, evaluates pass/fail criteria masks, and flags incomplete assessments
Declaration of Conformity: One-click PDF generation that compiles all assessment data into a structured regulatory document ready for CE marking
RedComply reduces EN 18031 compliance time by over 90%. Instead of spending months on spreadsheets and manual cross-referencing, your team can focus on the engineering decisions that actually require human expertise.
Visit redcomply.com to learn more and start your EN 18031 self-assessment today.