Assets: Security, Network, Privacy and Financial in EN 18031
If you are working on EN 18031 compliance (and therefore on RED regulations), there is one point that often trips up technical teams and documentation: the word "asset."
January 28, 2026
Introduction

If you are working on EN 18031 compliance (and therefore on RED regulations), there is one point that often trips up technical teams and documentation: the word "asset."
In common parlance, "asset" = "something of value."
In the EN 18031 standard, however, it is something much more specific: an asset is a target to be protected (or managed) because, if read, manipulated, or abused, it can have an impact on the network, security, or privacy.
And above all: we are not just talking about "data," but also about functions and configurations.
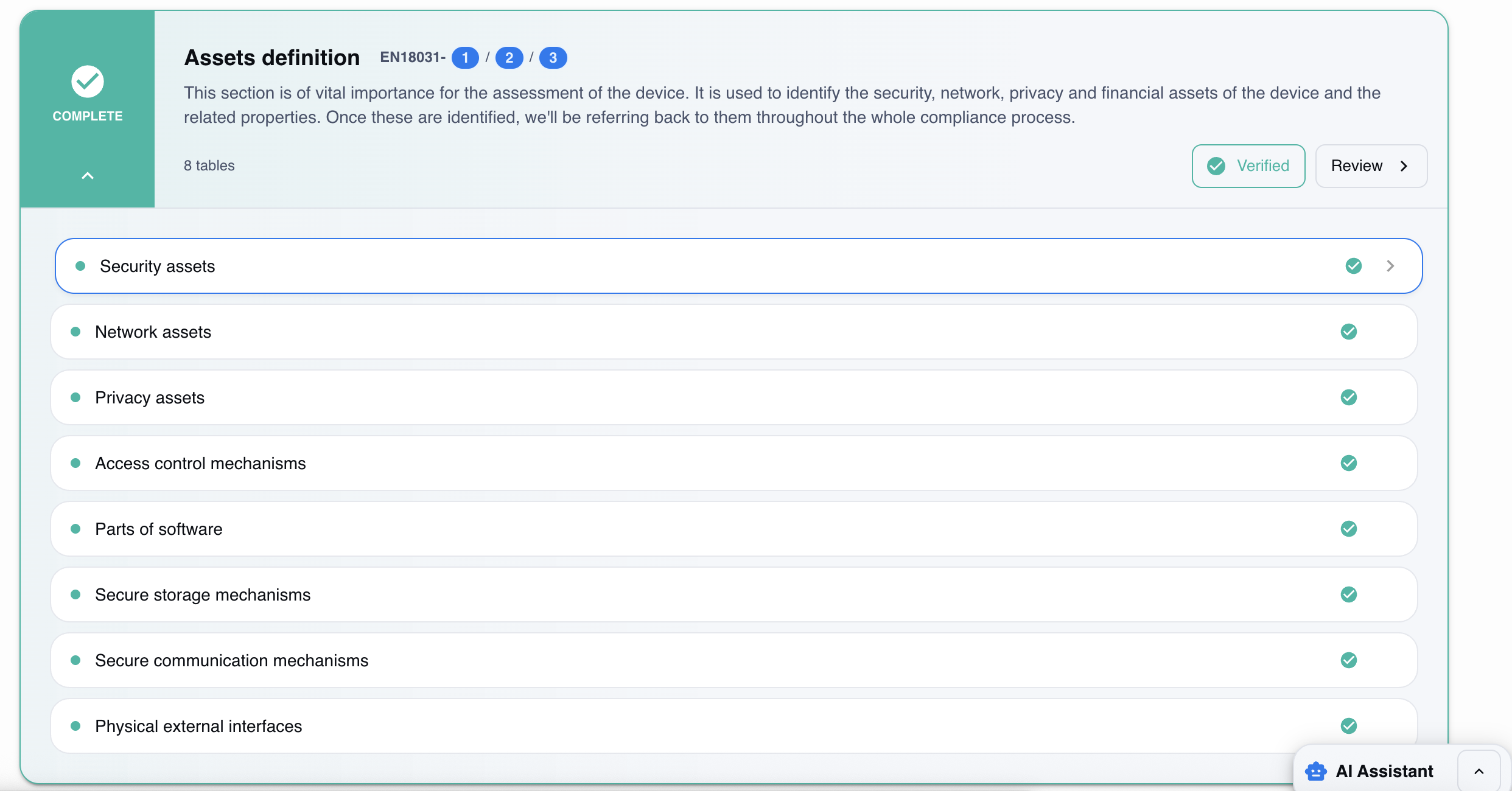
The standard distinguishes three main families which, depending on the part (Part 1 or Part 2), are combined in different ways:
Security assets (Part 1 and Part 2)
Network assets (Part 1)
Privacy assets (Part 2)
Financial assets (Part 3)
Understanding the difference is very important because it influences which mechanisms become applicable, what you need to put in technical documentation, and what tests a laboratory/assessor expects to see.
The pattern to know: asset = data + functions + configurations
Before delving into the three categories, let's establish the idea that EN 18031 formalizes that:
there are functions (security/network/privacy functions)
there are configurations that define the behavior of those functions (better known as function configuration)
This is why an "asset" is not just "a database" or "a file," but can also be an endpoint, a service, a setting, a mechanism (e.g., update), or a key.
This approach is explicit in the definitions and structure of the requirements (decision tree, required information per asset, assessment of completeness and sufficiency).
1) Security assets: everything that enables or supports security
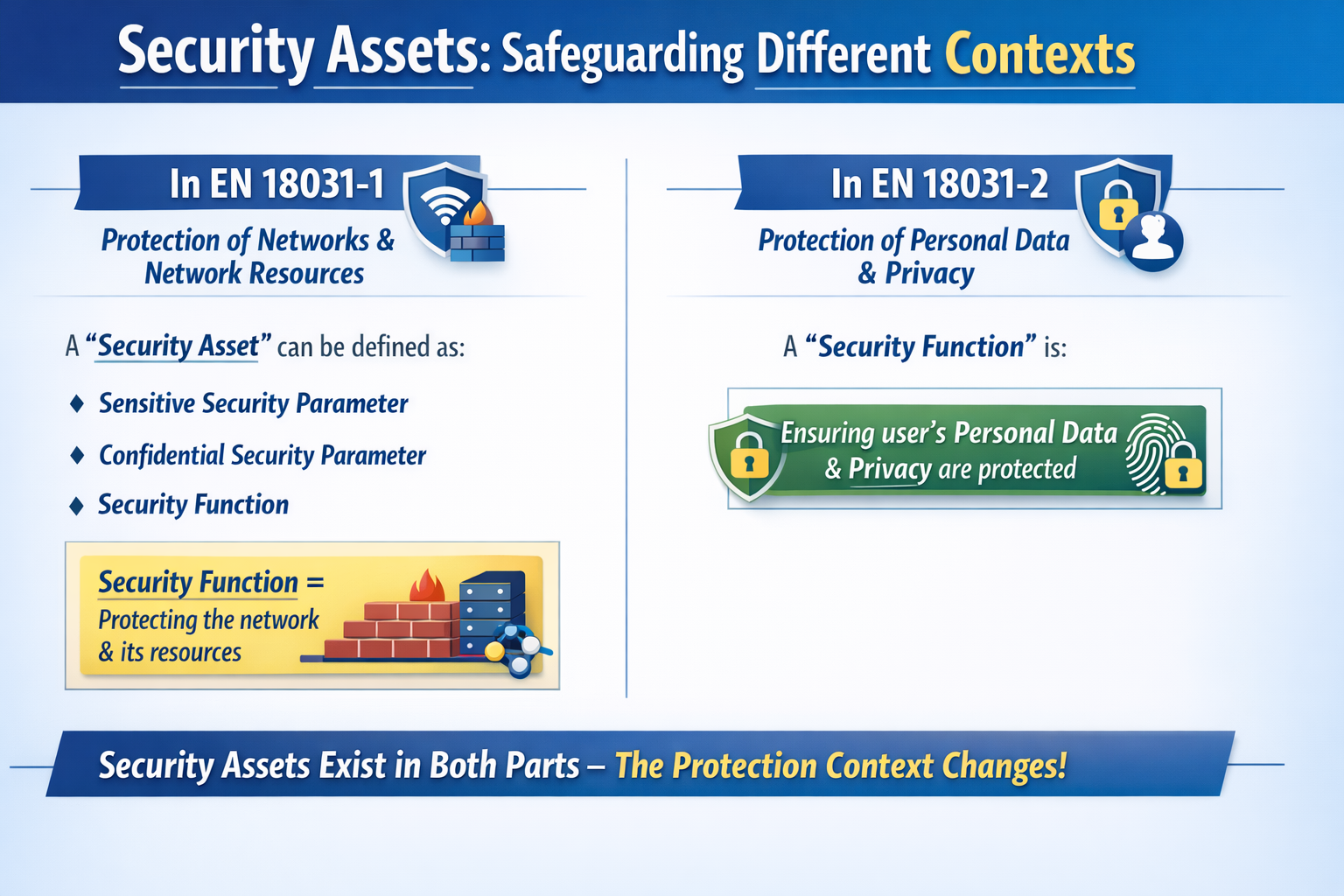
In the first part of the standard, namely EN 18031-1, a security asset can be defined in three ways:
sensitive security parameter
confidential security parameter
security function
The key concept to understand is that security is viewed from the perspective of protecting the network and network resources.
Thus, the security function is "the functionality of the equipment relevant to protecting it from damaging the network or abusing network resources."
In the second part of the standard, EN 18031-2, the definition of security function changes focus: it is a measure that ensures that the personal data and privacy of the user/subscriber are protected.
So "security assets" exist in both parts, and what changes is the context of protection.
Practical examples (almost always security assets)
Let's look at a few examples to give the reader a better understanding of what classic security assets might be:
administrative credentials or access tokens
cryptographic keys and PKI material
secure update mechanisms (integrity, authenticity, rollback, etc.)
parameters that, if manipulated, lower the security posture (debug enable, service exposure, etc.)
If a hacker obtains or alters these elements, they can "open the door" to other impacts: network abuse, pivoting, data access, etc.
For a complete walkthrough of security functions, security parameters (CSP and SSP), and a practical table-filling example, see our dedicated guide to security assets.
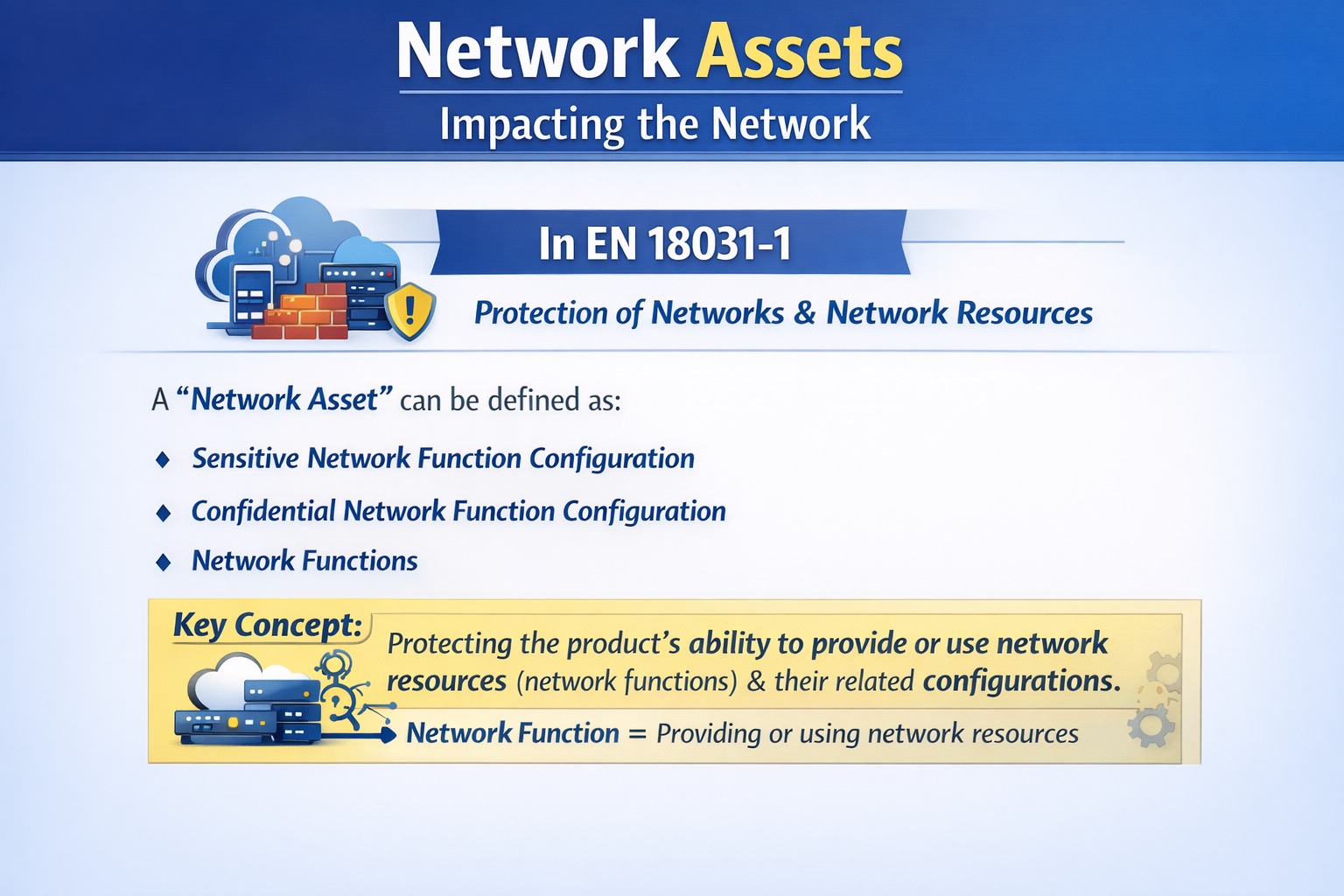
2) Network assets: what can damage the network
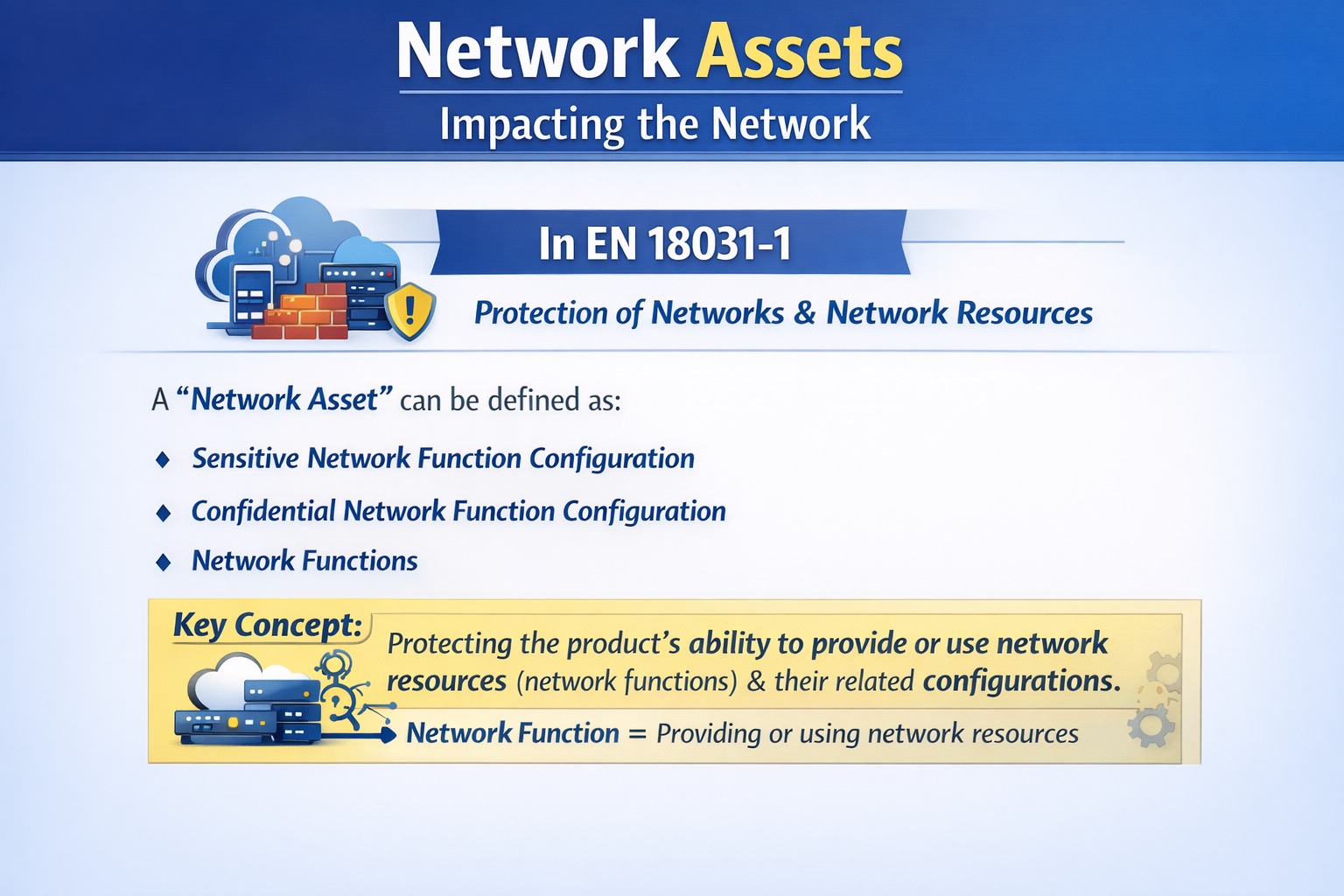
In the first part of the standard, namely EN 18031-1, a network asset can be defined in three ways:
sensitive network function configuration
confidential network function configuration
network functions
The key concept to understand is that it is not "the network" in the abstract that is being protected, but rather the product's ability to provide or use network resources (network functions) and their configurations.
Practical examples (typical network assets)
Let's look at a few examples to give the reader a better understanding of what classic network assets might be:
DNS/DHCP configuration, gateway, routing/NAT
VPN, APN, network firewall/ACL policy configurations
Features that generate or route traffic (e.g., router mode, bridge mode, hotspot)
parameters that, if manipulated, lead to DoS, internal scanning, amplification, bandwidth abuse
So, the basic concept to keep in mind when talking about network assets is that you need to think about the risk you may have "towards the outside" (network, infrastructure, consumed resources).
For step-by-step instructions on identifying and classifying network assets, see our detailed guide to network assets.
3) Privacy assets: personal data + processing functions and configurations
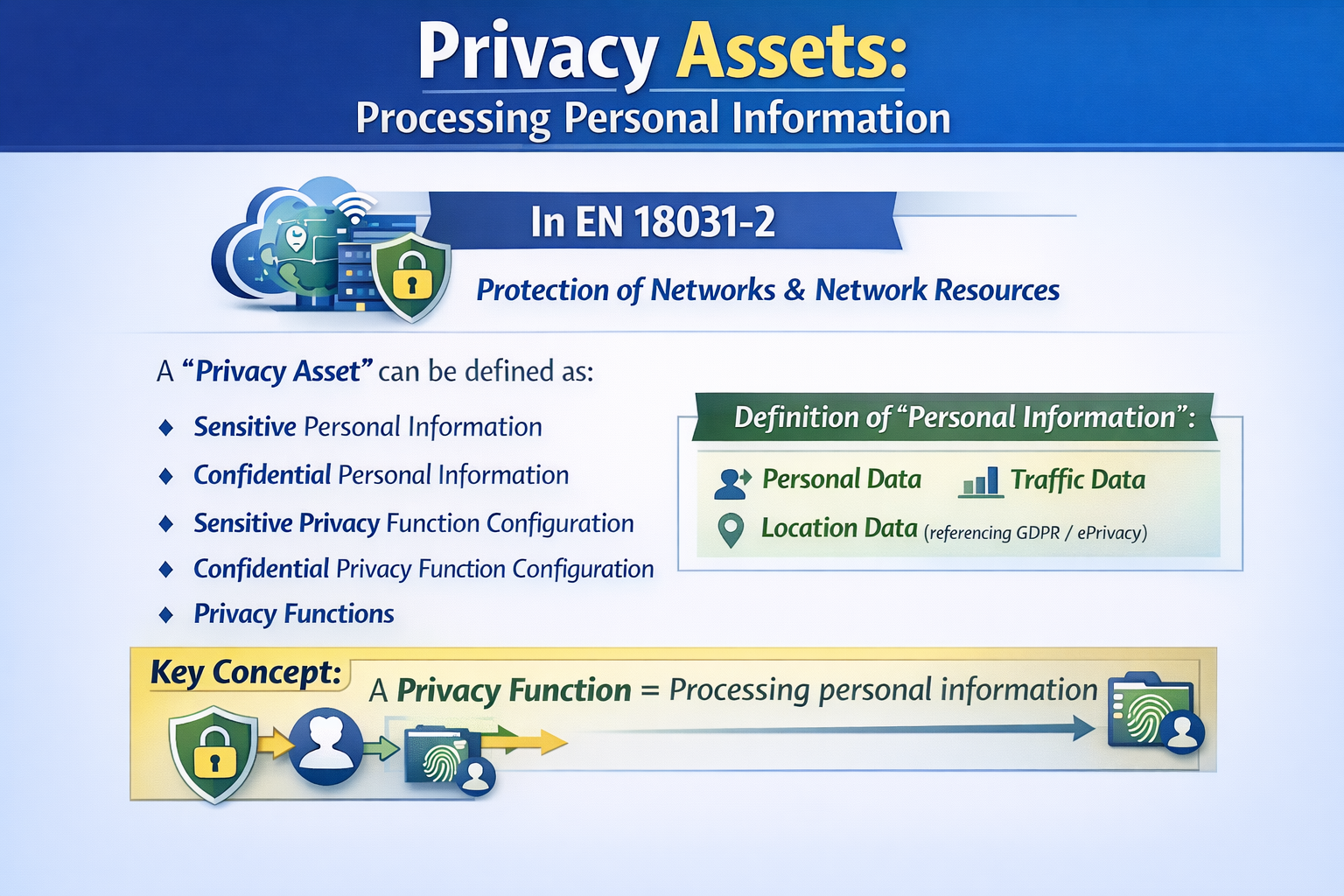
In the second part of the standard, namely EN 18031-2, a privacy asset can be defined in five ways:
sensitive personal information
confidential personal information
sensitive privacy function configuration
confidential privacy function configuration
privacy functions
Here, the standard is very clear, and "personal information" includes personal data, traffic data, and location data (references to GDPR/ePrivacy).
Therefore, a privacy function is nothing more than a feature that processes personal information.
Practical examples (typical privacy assets)
Let's look at a few examples to give the reader a better understanding of what classic privacy assets might be:
location data and location history
audio/video and associated metadata
address book, identifiers, telemetry with user ID
traffic data (e.g., who you contact, when, from where)
consent, retention, sharing, export, and deletion settings
A classic mistake that many people often make is to consider only the data (e.g., "geolocation") as a "privacy asset" and ignore the privacy function configuration (e.g., "location sharing ON by default," "365-day retention," "automatic upload").
We cover the full identification and documentation process in our guide to privacy assets.
4) Financial assets: everything that enables or supports transactions and value
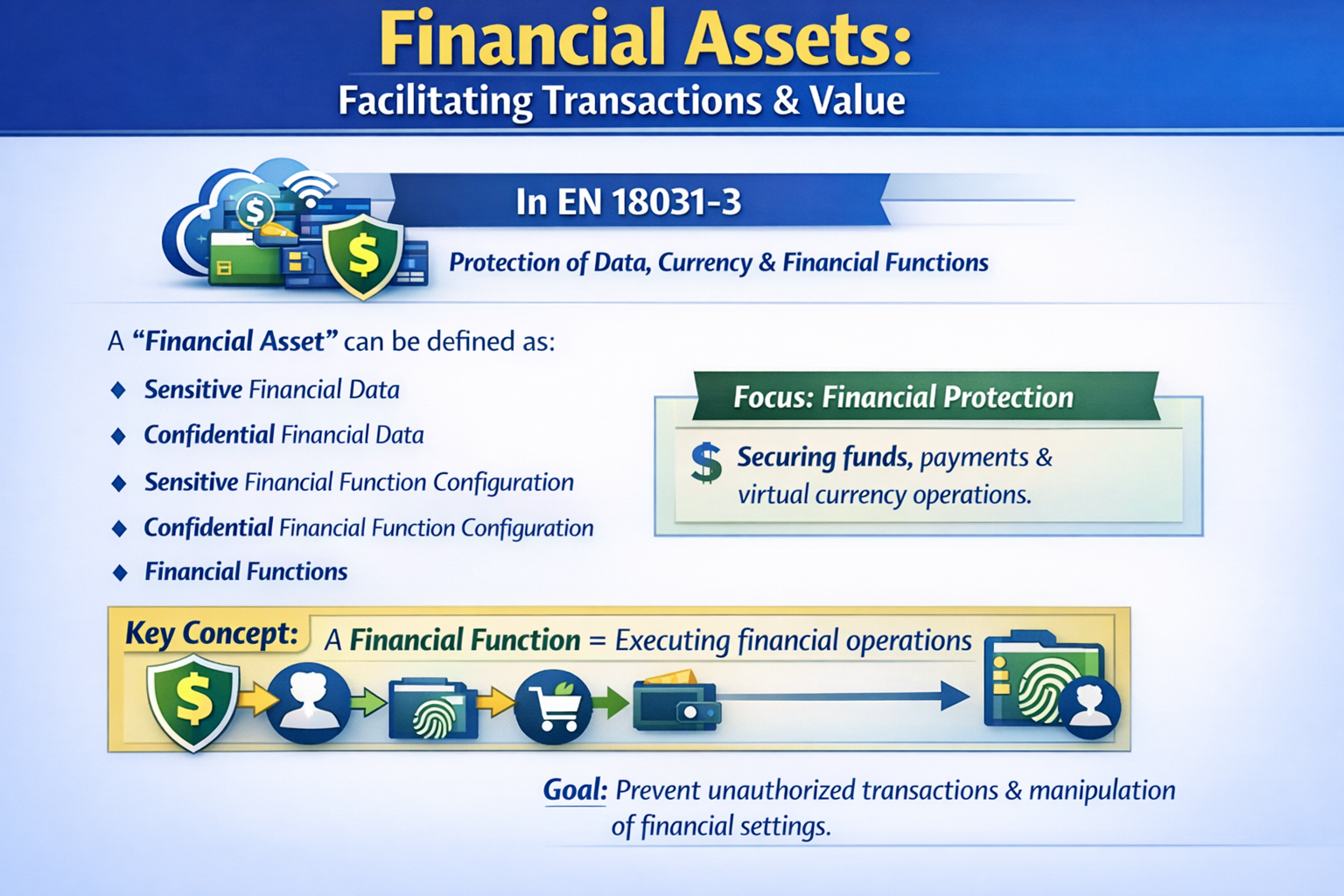
In the third part of the standard, namely EN 18031-3, a financial asset can be defined in five ways:
sensitive financial data
confidential financial data
sensitive financial function configuration
confidential financial function configuration
financial functions
The key concept to understand is that the part concerning financial assets is viewed from the perspective of protecting data and functions that manage money/value transfers (including virtual currencies) and the configurations that determine their behavior.
The goal is not "just" to protect data, but to prevent anyone from performing unauthorized financial transactions or manipulating parameters that make fraud or abuse possible.
Practical examples
Let's look at a few examples to better understand what classic financial assets might be:
payment data and transactional references (PAN/token, IBAN, transaction ID, order details)
credentials or secrets related to wallets and payments (PSP tokens, API keys, signature keys for authorizations)
payment, top-up, or transfer functions (checkout, in-app purchase, cash-out, top-up)
"sensitive" configurations of the financial function (limits, beneficiary whitelists, anti-fraud rules, PSP endpoints)
If a hacker obtains or alters these elements, the impact is immediate, such as theft of value, fraudulent payments, diversion of funds, or bypassing of controls (limits, authorizations, anti-fraud).
For a deep dive with practical examples, see our guide to financial assets according to EN 18031-3.
Let's take a moment to summarize the situation
So far, we have clarified what security assets, network assets, and privacy assets are, i.e., not just data, but functions and configurations that, if exposed or manipulated, change the risk of the product.
At this point, the question is: ok, so what?
The answer is that this taxonomy is not a "textbook" classification: in EN 18031, it is a compliance routing mechanism.
In other words, the asset category you identify determines:
which requirements become applicable
what evidence you need to produce
which tests you need to plan to demonstrate that those protections work.
1) From asset category to applicable requirements
Many of the requirements in EN 18031 are explicitly written in terms of assets.
For example, access control (ACM) in Part 1 is formulated to manage access to security assets and network assets, while in Part 2 the same concept applies to security assets and privacy assets.
Therefore, if you misclassify an item (or worse, omit it), you risk excluding the very controls that the standard expects from the perimeter.
2) From assets to documentation ("required information")
The standard does not ask you generically "do we have access control": it asks you for information for each accessible asset, i.e., a defensible description of:
which assets exist
how they are accessible
and what mechanisms protect them
3) From assets to testing: completeness and sufficiency
Finally, asset classification also guides how an assessor evaluates tests. Typically, there are two levels:
completeness: have you identified and declared all relevant assets/interfaces?
sufficiency: are the protections implemented actually adequate for the declared assets?
If you have classified the assets incorrectly, you already fail due to lack of completeness, and the assessor finds a service, an endpoint, an undocumented configuration, and the chain of evidence is broken.
A simple way to classify: 3 questions
One of the questions our customers often ask us is: "How can I decide whether a piece of data is a security/network/privacy/financial asset?"
For simplicity's sake, we suggest using this triage:
1. Is it a network function or configuration (providing/utilizing network resources)?
If the answer is "Yes," then it is a network asset.
2. Is it a security parameter/function (keys, credentials, protection mechanisms)?
If the answer is "Yes," then it is a security asset.
3. Is it personal information or a function/configuration that processes it?
If the answer is "Yes," then it is a Privacy asset.
4. Is it financial data/function/configuration that enables or governs payments or transfers of value (e.g., checkout, wallet, limits, tokens/transaction IDs)?
If the answer is "Yes," then it is a Financial asset.
If it falls into multiple categories, then you can treat it as a "multi-asset," which means you will need to apply more conservative controls and tests.
Asset taxonomy is the basis of compliance
In EN 18031, the distinction between security, network, and privacy assets is a compliance routing mechanism because it defines what you need to protect, how you need to document it, and how you need to demonstrate it.
To summarize what we have said and create a basic mental framework, you can divide the three assets as follows:
Security assets: what is needed to keep the system secure (security functions/parameters).
Network assets: what can impact the network or its resources (network functions/configurations)
Privacy assets: what impacts user/subscriber privacy (personal data + processing functions/configurations).
Financial assets: what enables or governs payments, financial transactions, or transfers of value (financial data + payment functions/configurations, wallets, limits, authorizations).
How RedComply manages the entire process
As of August 1, 2025, RED compliance has become mandatory.
All the assets we have discussed must be identified before any other section of the Technical Documentation, and it is important to do everything possible to avoid incurring penalties.
Identifying security assets on real firmware requires specific skills: binary analysis, network scanning, startup script review, dependency mapping.
Done manually, it takes weeks.
Our RedComply platform speeds up the compilation of security and all RED regulations by over 90%.
This is because RedComply automates the most labor-intensive parts of the process.
For example, you can upload the firmware and obtain an initial automatic mapping of all Asset Parameters in just a few days, achieving compliance with EN 18031 in no time.
Request a demo and our team will contact you to help you!
RedComply reduces EN 18031 compliance times by over 90%. Learn more at redcomply.com.