Essential Cybersecurity Standards for IoT
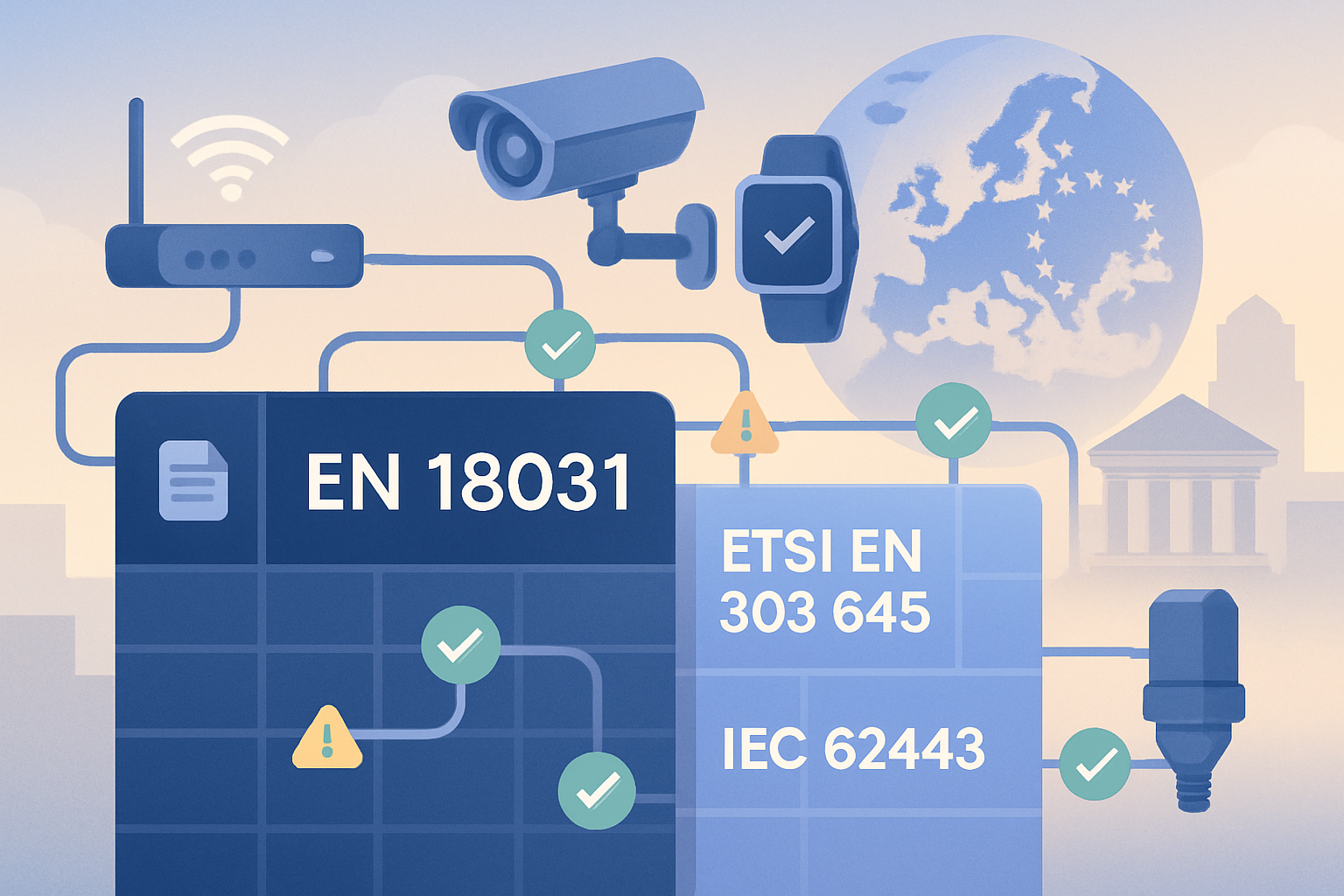
The IoT cybersecurity landscape is shaped by several key standards, each targeting different markets, device types, and risk profiles. For manufacturers selling internet-connected devices in the EU, understanding which standards apply and how they interact is the first step toward compliance and market access.
March 21, 2026
Key Takeaways

IoT cybersecurity standards define the minimum security requirements that connected devices must meet before reaching consumers and enterprises. For EU-focused manufacturers, the most critical standard is EN 18031, which provides a presumption of conformity with the RED Directive's cybersecurity provisions. But it is not the only standard that matters.
EN 18031 is the harmonised European standard for RED cybersecurity compliance, covering network security (Part 1), privacy protection (Part 2), and fraud prevention (Part 3).
ETSI EN 303 645 defines a baseline for consumer IoT security and is widely referenced but does not provide RED presumption of conformity.
IEC 62443 targets industrial IoT and operational technology environments with a comprehensive multi-level security framework.
NIST IR 8425 provides a US-focused IoT core baseline for consumer devices, useful as a reference but not applicable for EU regulatory compliance.
For EU market access, EN 18031 is currently the most direct and practical compliance pathway under the Radio Equipment Directive.
The Global Landscape of IoT Cybersecurity Standards
IoT cybersecurity standards have emerged from different regulatory bodies worldwide, each addressing specific aspects of device security. Understanding the landscape helps manufacturers prioritise efforts and avoid duplicating work across overlapping frameworks.
| Standard | Scope | Geography | Status | RED Presumption |
|---|---|---|---|---|
EN 18031 (Parts 1-3) | Radio equipment cybersecurity | EU | Harmonised standard | Yes |
ETSI EN 303 645 | Consumer IoT baseline security | EU / Global | Published standard | No |
IEC 62443 | Industrial automation and control | Global | Published standard | No |
NIST IR 8425 / 8259 | Consumer IoT core baseline | US | Published guidance | No |
ISO/IEC 27400 | IoT security and privacy guidelines | Global | Published standard | No |
Why does the RED presumption of conformity matter?
The Radio Equipment Directive (RED) requires all internet-connected radio equipment sold in the EU to meet cybersecurity requirements under Articles 3.3(d), 3.3(e), and 3.3(f). A harmonised standard provides a presumption of conformity: if your device meets EN 18031, it is presumed to satisfy the RED cybersecurity requirements. No other IoT standard currently offers this presumption.
This does not mean other standards are irrelevant. ETSI EN 303 645 is valuable as a security baseline and can inform your EN 18031 documentation. IEC 62443 is essential for industrial devices. But for regulatory compliance with the RED Directive, EN 18031 is the standard that matters most.
For a focused introduction to the RED cybersecurity regulation and its requirements, see our RED cybersecurity overview.
EN 18031: The EU's Harmonised Standard for RED Cybersecurity

EN 18031 is divided into three parts, each mapping to a specific RED article. Manufacturers must comply with the parts that match their device's capabilities and intended use:
| EN 18031 Part | RED Article | Focus Area | Applies When |
|---|---|---|---|
EN 18031-1 | Article 3.3(d) | Network security | Device connects to the internet or a network |
EN 18031-2 | Article 3.3(e) | Privacy and data protection | Device processes personal data |
EN 18031-3 | Article 3.3(f) | Fraud prevention | Device handles financial transactions or virtual currency |
What does EN 18031 compliance involve?
EN 18031 compliance is a structured documentation process. For each applicable part, manufacturers must:
Identify security assets: Catalogue all security functions (features that protect something) and security parameters (data that defines how those functions behave) on the device.
Complete compliance tables: Populate structured data grids covering equipment identification, access control mechanisms, cryptographic implementations, vulnerability handling, software update mechanisms, and more.
Navigate decision trees: Answer branching yes/no questionnaires that determine whether specific requirements are met, resulting in PASS, FAIL, or NOT_ASSESSED outcomes.
Execute the test plan: Complete a three-tier assessment (Conceptual Assessment, Functional Sufficiency, Functional Completeness) with documented verdicts.
Generate the Declaration of Conformity (DoC): Compile all results into the structured PDF document required for EU market access.
Key compliance domains in EN 18031
EN 18031 organises requirements into several domains that must be assessed:
Equipment Identification: Unique identification of the device and its components
Access Control Mechanisms: Authentication, authorisation, and session management
Cryptography: Encryption algorithms, key management, and secure communications
Vulnerability Handling: Processes for identifying, reporting, and remediating vulnerabilities
Software Update Mechanisms: Secure delivery, verification, and rollback of firmware and software updates
Logging and Monitoring: Security event recording and network activity awareness
Secure Boot and Integrity: Boot process protection and software integrity verification
Other Standards You Should Know
ETSI EN 303 645: The Consumer IoT Baseline
ETSI EN 303 645 was one of the first European standards specifically addressing consumer IoT security. It defines 13 provisions covering areas like default password elimination, secure communications, software update mechanisms, and vulnerability disclosure. While it does not provide a presumption of conformity with the RED Directive, it remains a widely referenced baseline that influenced EN 18031's development.
For manufacturers already familiar with ETSI EN 303 645, the transition to EN 18031 involves deepening the documentation and adding structured assessment workflows (decision trees, test plans) that ETSI EN 303 645 does not require.
IEC 62443: Industrial IoT and OT Security
IEC 62443 is the gold standard for industrial automation and control system security. It uses a zone-and-conduit model with four security levels (SL-1 through SL-4), providing a comprehensive framework for industrial IoT environments. If your device operates in industrial settings, IEC 62443 compliance may be required by your customers regardless of RED requirements.
IEC 62443 and EN 18031 can coexist: a device might need IEC 62443 for its industrial customers and EN 18031 for EU market access. Many security controls overlap, which can reduce the documentation burden when pursuing both.
NIST IR 8425 and the US IoT Baseline
The NIST Cybersecurity for IoT Program published NIST IR 8425 as a profile of the IoT Core Baseline specifically for consumer products. It defines minimum cybersecurity capabilities including asset identification, data protection, interface access control, and software update requirements. While US-focused and non-binding for EU compliance, it provides a useful reference for manufacturers selling in both markets.
ISO/IEC 27400: IoT Security and Privacy Guidelines
ISO/IEC 27400 provides guidelines for IoT security and privacy within the broader ISO 27000 family. It is a guidance document rather than a certification standard, offering best practices for IoT risk management, data handling, and device lifecycle security. It complements EN 18031 by providing a broader security management perspective.
Compliance Checklist: Getting Started with EN 18031

For product security managers and compliance engineers beginning their EN 18031 journey, here is a practical checklist to guide your preparation:
Determine which EN 18031 parts apply: Does your device connect to a network (Part 1)? Process personal data (Part 2)? Handle financial transactions (Part 3)? Most consumer IoT devices require at least Part 1.
Inventory your security assets: Identify all security functions (authentication mechanisms, encryption libraries, firewalls) and security parameters (keys, certificates, configuration policies) on the device.
Map your device architecture: Document how security functions and parameters interact, which network interfaces exist, and where data flows.
Review each compliance domain: Work through equipment identification, access control, cryptography, vulnerability handling, software updates, and logging sections systematically.
Complete decision trees for each requirement: Navigate the branching assessments to determine PASS/FAIL outcomes for every applicable requirement.
Execute the three-tier test plan: Complete Conceptual Assessment, Functional Sufficiency Assessment, and Functional Completeness Assessment with documented verdicts.
Generate your Declaration of Conformity: Compile all assessment results into the structured DoC document.
Establish ongoing maintenance processes: Plan for re-assessment when firmware updates or hardware changes affect security-relevant functions.
Common pitfalls to avoid
Starting too late: EN 18031 compliance requires significant documentation effort. Begin the process early in product development, not weeks before market launch.
Ignoring asset identification: Security asset identification is the mandatory first step. Without it, you cannot determine which requirements apply to your device.
Treating compliance as a checkbox exercise: EN 18031 requires substantive technical justifications, not just yes/no answers. Auditors will examine the quality of your documentation.
Overlooking multi-standard interactions: If your device needs both EN 18031 and IEC 62443, plan your documentation strategy to leverage overlapping controls.
Frequently Asked Questions
Is EN 18031 mandatory for all IoT devices sold in the EU?
Yes. Since 1 August 2025, the RED Directive cybersecurity requirements under Articles 3.3(d), 3.3(e), and 3.3(f) are mandatory for internet-connected radio equipment placed on the EU market. EN 18031 is the harmonised standard that provides a presumption of conformity with those requirements. While manufacturers could theoretically use alternative means to demonstrate compliance, EN 18031 is in practice the required pathway - it is the only harmonised standard mapped to these articles, making it the clearest and most widely accepted approach.
What is the difference between EN 18031 and ETSI EN 303 645?
ETSI EN 303 645 defines a baseline of 13 security provisions for consumer IoT. EN 18031 is a more comprehensive harmonised standard that provides a presumption of conformity with the RED Directive. EN 18031 requires structured compliance tables, decision trees, a three-tier test plan, and a Declaration of Conformity, all of which go beyond what ETSI EN 303 645 asks for. Think of ETSI EN 303 645 as a foundation and EN 18031 as the complete compliance framework.
Can I use IEC 62443 instead of EN 18031 for EU market access?
No. IEC 62443 is an excellent industrial security standard, but it does not provide a presumption of conformity with the RED Directive. For EU market access of radio equipment, you need to demonstrate compliance with RED Articles 3.3(d), 3.3(e), and/or 3.3(f). EN 18031 is currently the only harmonised standard that provides this presumption. However, if you already have IEC 62443 documentation, much of the technical evidence can be reused in your EN 18031 assessment.
How do US and EU IoT cybersecurity standards compare?
The US approach (NIST IR 8425, NIST Cybersecurity Framework) is guidance-based and largely voluntary for consumer IoT, though mandatory for US federal procurement. The EU approach under the RED Directive is regulatory and mandatory for market access. Both share similar security principles (access control, software updates, vulnerability management), but the EU requires formal conformity assessment documentation. Manufacturers selling in both markets should align their security architecture with both frameworks but need EN 18031 specifically for EU regulatory compliance.
When do the RED cybersecurity requirements take effect?
The RED cybersecurity requirements under Delegated Regulation (EU) 2022/30 activating Articles 3.3(d), 3.3(e), and 3.3(f) apply to radio equipment placed on the EU market. Manufacturers should already be preparing their compliance documentation using EN 18031 to ensure timely market access. The enforcement timeline means that devices placed on the market must meet these requirements, making early preparation essential.
Conclusion: Choosing the Right Standards for Your IoT Device
The essential cybersecurity standards for IoT form a layered ecosystem. EN 18031 stands at the center for any manufacturer targeting the EU market with internet-connected radio equipment. It is the only standard that provides a presumption of conformity with the RED Directive's cybersecurity provisions under Articles 3.3(d), 3.3(e), and 3.3(f).
Complementary standards like ETSI EN 303 645, IEC 62443, and NIST IR 8425 serve important roles in specific contexts, whether as a consumer IoT baseline, an industrial security framework, or a US regulatory reference. But none replaces EN 18031 for EU compliance.
The practical takeaway for product security managers and compliance engineers is clear: start with EN 18031, identify which parts apply to your device, inventory your security assets, and work systematically through the compliance domains. Early preparation, structured documentation, and the right tools make the difference between a smooth market launch and costly delays.
The regulatory landscape extends beyond standards to legislation. Our article on preparing for new EU cybersecurity regulations covers how RED, CRA, and NIS2 interact.
Getting Started with RedComply
RedComply is the compliance automation platform purpose-built for EN 18031 and the RED Directive. Instead of managing compliance in spreadsheets or generic GRC tools, RedComply provides the exact structure that EN 18031 requires: guided compliance tables, interactive decision trees, auto-calculated test plans, and one-click Declaration of Conformity generation.
Here is how to get started:
Create a project and select which EN 18031 parts apply to your device (Part 1, Part 2, Part 3, or any combination)
Add your device and identify your security assets with structured tables that guide you through every category
Work through compliance sections with decision trees that navigate complex requirements and record outcomes automatically
Generate your test plan with auto-calculated verdicts across all three assessment tiers
Export your Declaration of Conformity as a structured PDF ready for regulatory review
An integrated AI assistant with deep knowledge of EN 18031 is available throughout, helping you search the standard, answer context-specific questions, and maintain consistency across your entire compliance documentation. Visit redcomply.com to start your EN 18031 compliance journey.