How to Prepare for New EU Cybersecurity Regulations
The EU is enforcing a new wave of cybersecurity regulations that directly affect manufacturers of internet-connected devices. RED cybersecurity requirements are already mandatory since August 2025, the Cyber Resilience Act is next, and market surveillance audits could begin at any time. Here is what you need to know and do now.
March 31, 2026
Key Takeaways

Preparing for EU cybersecurity regulations means understanding which rules apply to your product, identifying the compliance gaps in your current processes, and building a structured documentation workflow that satisfies the technical requirements of standards like EN 18031. The regulations are not optional - they are mandatory for EU market access.
Three major regulations matter now: The RED Directive (Delegated Regulation (EU) 2022/30), the Cyber Resilience Act (CRA), and the NIS2 Directive each impose cybersecurity obligations on different product and service categories.
EN 18031 is the compliance pathway for radio equipment: This harmonised European standard (parts 1, 2, and 3) provides a presumption of conformity with RED Articles 3.3(d), 3.3(e), and 3.3(f).
Preparation starts with gap analysis: Before writing documentation, manufacturers must map their products against the applicable regulations and identify which requirements are already met and which need work.
Structured documentation is non-negotiable: Compliance requires detailed technical documentation - asset inventories, compliance tables, decision tree assessments, test plans, and a Declaration of Conformity (DoC).
RED is already mandatory: RED cybersecurity requirements under Delegated Regulation (EU) 2022/30 have been mandatory since 1 August 2025. Market surveillance audits could begin at any time. The Cyber Resilience Act has a phased timeline extending to 2027.
The EU Cybersecurity Regulatory Landscape Explained

The EU has introduced several overlapping cybersecurity regulations targeting different aspects of the digital economy. For manufacturers of internet-connected devices, three frameworks are most relevant.
The Radio Equipment Directive (RED) - Delegated Regulation (EU) 2022/30
The RED Directive is the primary regulation for radio equipment sold in the EU. Delegated Regulation (EU) 2022/30 activated three new cybersecurity essential requirements:
Article 3.3(d): Network protection - radio equipment must not harm the network or its functioning, nor misuse network resources
Article 3.3(e): Privacy and personal data protection - safeguards for personal data and privacy of users
Article 3.3(f): Fraud prevention - protection against fraud, including features to ensure authenticated and authorized financial transactions
These requirements became applicable on 1 August 2025. Any radio equipment placed on the EU market after that date must demonstrate compliance.
For a focused introduction to the RED cybersecurity requirements and compliance steps, see our RED cybersecurity overview.
EN 18031: The Harmonised Standard for RED Cybersecurity
EN 18031 is a three-part harmonised European standard that provides the most practical compliance path for the RED cybersecurity requirements:
EN 18031-1: Addresses Article 3.3(d) - network security requirements
EN 18031-2: Addresses Article 3.3(e) - privacy and data protection requirements
EN 18031-3: Addresses Article 3.3(f) - fraud prevention requirements
Following EN 18031 provides a presumption of conformity - meaning that if your product meets the standard's requirements, it is presumed to satisfy the corresponding RED articles. This is currently the most efficient pathway for manufacturers.
The Cyber Resilience Act (CRA)
The Cyber Resilience Act (Regulation (EU) 2024/2847) is a broader horizontal regulation covering all products with digital elements. It introduces mandatory cybersecurity requirements across the entire product lifecycle, including vulnerability handling, security updates, and incident reporting obligations.
The CRA has a phased timeline: vulnerability reporting obligations apply from September 2026, and full compliance requirements apply from December 2027. For products already covered by the RED Directive, the two frameworks will eventually converge - but the RED cybersecurity requirements apply first.
NIS2 Directive
The NIS2 Directive (Directive (EU) 2022/2555) focuses on network and information security for essential and important entities - primarily service providers and infrastructure operators rather than product manufacturers. However, manufacturers whose products serve critical infrastructure sectors may face indirect requirements through their customers' NIS2 obligations.
Step-by-Step Preparation Checklist

Preparing for EU cybersecurity regulations is a structured process. Here is a practical checklist that product security managers and compliance engineers can follow.
Phase 1: Scoping and Gap Analysis
Identify which regulations apply: Determine whether your product falls under RED (radio equipment), CRA (products with digital elements), or both. Many IoT devices are subject to multiple frameworks.
Map your product portfolio: List all products and variants that require EU market access. Group them by architecture similarity - products sharing similar security designs can share compliance work.
Select applicable EN 18031 parts: Based on your product's functionality, determine which parts of EN 18031 apply (1, 2, 3, or any combination).
Conduct a preliminary gap analysis: Compare your current security measures against EN 18031 requirements. Identify which sections (access control, cryptography, vulnerability handling, software updates, etc.) need attention.
Phase 2: Security Asset Identification
Identify security functions: Document all device features that serve a protective purpose - cryptographic libraries, authentication mechanisms, firewalls, secure boot, encrypted communications.
Identify security parameters: Document the data that controls security behavior - keys, certificates, passwords, configuration files, access control lists.
Map the relationships: Every security parameter must be linked to the security function it supports. The documentation must show these connections explicitly.
Build your asset inventory: Create a structured inventory of all security assets. This inventory feeds into every subsequent compliance step.
Phase 3: Compliance Documentation
Work through compliance sections: EN 18031 organizes requirements into sections - Equipment Identification, Access Control Mechanisms, Vulnerability Handling, Cryptography, Software Update Mechanisms, Logging, and more.
Complete compliance tables: Each section contains structured tables where you document how your product meets specific requirements. This includes descriptions, justifications, and evidence references.
Navigate decision trees: Many requirements use decision trees - structured yes/no question sequences that lead to PASS, FAIL, or NOT_ASSESSED outcomes for each requirement.
Build the test plan: Complete the three-tier assessment - Conceptual Assessment, Functional Sufficiency Assessment, and Functional Completeness Assessment.
Phase 4: Validation and Declaration
Review for completeness: Verify that all applicable sections, tables, and decision trees are completed. Check that no requirements are left without justification.
Generate the Declaration of Conformity: Compile all compliance data into a structured DoC PDF - the official document required for EU market access.
Determine the conformity assessment route: Decide whether self-assessment is sufficient or whether a Notified Body review is required for your product category.
Maintain living documentation: Compliance is not a one-time event. Product updates, new firmware versions, and architecture changes require re-evaluation of affected sections.
RED Directive vs. Cyber Resilience Act: Which Applies to You?
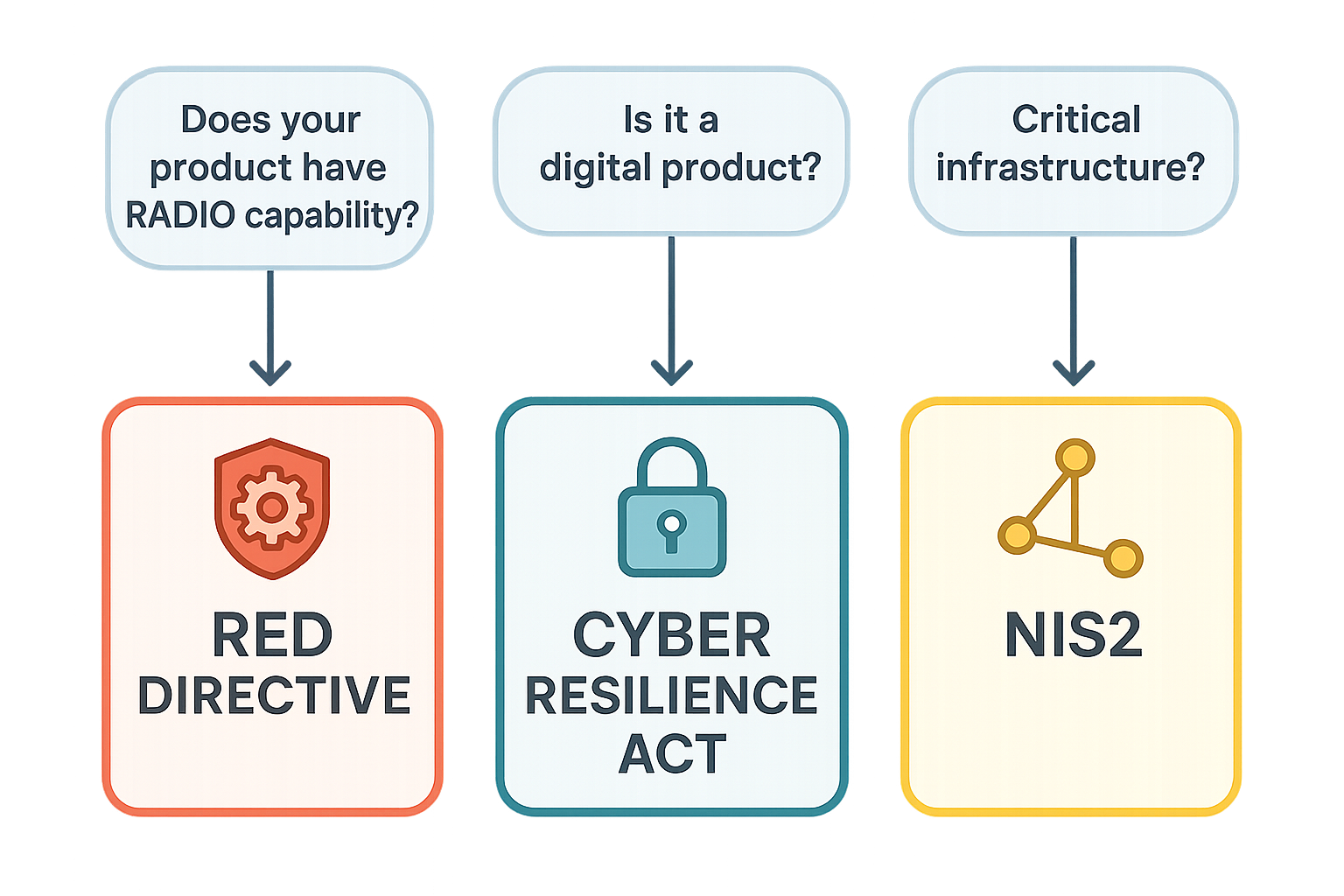
One of the most common sources of confusion is understanding which EU cybersecurity regulation applies to a specific product. Here is a comparison of the three main frameworks.
| Aspect | RED Directive (2022/30) | Cyber Resilience Act | NIS2 Directive |
|---|---|---|---|
Scope | Radio equipment (devices with radio transmitters/receivers) | All products with digital elements | Essential and important service entities |
Target | Product manufacturers | Product manufacturers | Service providers and operators |
Cybersecurity articles | Articles 3.3(d), 3.3(e), 3.3(f) | Annex I essential requirements | Risk management and incident reporting |
Harmonised standard | EN 18031 (parts 1, 2, 3) | Under development | N/A (organizational measures) |
Applicable from | 1 August 2025 | Phased: Sep 2026 - Dec 2027 | October 2024 (transposition) |
Conformity route | Self-assessment or Notified Body | Self-assessment, third-party, or EU type examination | Supervisory authority oversight |
Documentation output | Declaration of Conformity + technical documentation | Technical documentation + SBOM | Security policies and incident reports |
What if my product falls under both RED and CRA?
Many IoT devices - particularly those with Wi-Fi, Bluetooth, Zigbee, or cellular connectivity - fall under both the RED Directive and the Cyber Resilience Act. In practice, this means:
RED cybersecurity requirements apply first (from August 2025), using EN 18031 as the compliance pathway
CRA requirements will layer on top (from 2027), potentially requiring additional documentation such as a Software Bill of Materials (SBOM)
Compliance work is largely complementary: Security measures documented for EN 18031 will satisfy many CRA requirements as well, reducing duplication
Start with EN 18031: Since RED deadlines are earlier, building your compliance foundation on EN 18031 is the most practical approach
EN 18031: The Practical Path for Radio Equipment Compliance
For product security managers working on radio equipment, EN 18031 is where preparation becomes concrete. The standard translates abstract cybersecurity requirements into structured, assessable criteria.
What EN 18031 covers
EN 18031 organizes cybersecurity requirements into clearly defined sections. Each section addresses a specific security domain:
Equipment Identification: Documenting what the device is, its hardware/software components, and radio module details
Access Control Mechanisms: How the device manages authentication, authorization, and privilege levels
Vulnerability Handling: Processes for identifying, tracking, and mitigating security vulnerabilities
Cryptography: Which cryptographic algorithms, protocols, and key management practices the device employs
Software Update Mechanisms: How firmware and software updates are securely delivered, verified, and applied
Logging and Monitoring: What security events the device records and how monitoring is implemented
Network Security: Protections against network-level attacks, traffic filtering, and secure communication
The documentation workflow
The EN 18031 compliance workflow follows a consistent pattern for each section:
Identify relevant assets: Which security functions and parameters are involved in this section
Complete compliance tables: Document how each requirement is met, with justifications and evidence
Navigate decision trees: Answer structured assessment questions to determine PASS/FAIL outcomes
Execute the test plan: Run the three-tier assessment (Conceptual, Functional Sufficiency, Functional Completeness)
Record outcomes: All results feed into the final Declaration of Conformity
Multi-standard scoping
A single product may need to comply with one, two, or all three parts of EN 18031. The standard uses a field inheritance system - sections, tables, and even individual columns are tagged with which parts they belong to. A project targeting EN 18031-1 and EN 18031-3 (but not -2) will only see requirements relevant to network security and fraud prevention, automatically excluding privacy-specific sections.
EN 18031 exists alongside other IoT standards. For a comparison with ETSI EN 303 645, IEC 62443, and others, see our guide to essential IoT cybersecurity standards.
Common Mistakes and How to Avoid Them
Based on real-world compliance efforts, here are the most common pitfalls manufacturers encounter when preparing for EU cybersecurity regulations.
1. Waiting for final guidance before starting
Some manufacturers delay preparation hoping for further clarification from regulatory bodies. This is risky - the RED cybersecurity requirements are already applicable. Even where harmonised standards are still being refined, the underlying essential requirements are fixed. Starting with EN 18031 now provides a solid foundation that can be adjusted as the landscape evolves.
2. Treating compliance as a one-time project
Cybersecurity compliance is ongoing. Every firmware update, architecture change, or new product variant potentially affects your compliance status. Build processes that allow compliance documentation to be maintained and updated - not just created once and forgotten.
3. Skipping the asset identification phase
Security asset identification is the mandatory first step of EN 18031 compliance. Without a complete inventory of security functions and security parameters, it is impossible to know which requirements apply. Rushing past this phase leads to incomplete documentation and gaps that emerge during assessment.
4. Using generic GRC tools for EN 18031
General-purpose Governance, Risk, and Compliance (GRC) platforms are designed for frameworks like ISO 27001 or SOC 2. They lack the specific structures that EN 18031 requires - decision trees, multi-standard filtering, test plan auto-calculation, and Declaration of Conformity generation. Purpose-built tooling saves significant time and reduces errors.
5. Ignoring multi-standard overlap
Products subject to both RED and CRA share many requirements. Manufacturers who address each regulation in isolation duplicate work and risk inconsistencies. A unified compliance strategy that recognizes overlap is more efficient and produces more coherent documentation.
Frequently Asked Questions
When do the new EU cybersecurity requirements take effect?
The RED cybersecurity requirements under Delegated Regulation (EU) 2022/30 became applicable on 1 August 2025. The Cyber Resilience Act has a phased timeline: vulnerability reporting from September 2026, and full compliance from December 2027. The NIS2 Directive required member state transposition by October 2024.
Does my product need to comply with both RED and CRA?
If your product is radio equipment (Wi-Fi, Bluetooth, cellular, etc.) and contains digital elements, it likely falls under both. The RED requirements apply first (August 2025), and CRA requirements add additional obligations from 2027. The good news is that compliance work for EN 18031 substantially overlaps with CRA requirements.
Can I self-assess or do I need a Notified Body?
For the RED Directive, most manufacturers can use self-assessment (internal production control) if they follow a harmonised standard like EN 18031. However, some product categories - particularly those with higher risk profiles - may require assessment by a Notified Body. The CRA also defines product categories (default, important, critical) with different conformity assessment routes.
What is the relationship between EN 18031 and the Cyber Resilience Act?
EN 18031 is a harmonised standard specific to the RED Directive - it provides a presumption of conformity with RED Articles 3.3(d), 3.3(e), and 3.3(f). The CRA will eventually have its own harmonised standards. However, the security measures documented under EN 18031 (access control, cryptography, vulnerability handling, software updates) align closely with CRA requirements, making the transition smoother.
How long does it take to prepare for EN 18031 compliance?
The timeline depends on the product's complexity and the manufacturer's existing security maturity. A straightforward IoT device with well-documented security measures may require 4 to 8 weeks for full documentation using structured tooling. More complex products with multiple communication interfaces, extensive software stacks, or multiple EN 18031 parts may take longer. Starting with a gap analysis provides the most realistic estimate for your specific situation.
Conclusion: Start Now, Build on EN 18031
The question is no longer whether EU cybersecurity regulations will affect your products - it is how prepared you are when enforcement arrives. For manufacturers of radio equipment and IoT devices, the answer is clear: start with EN 18031.
EN 18031 provides the most structured, well-defined compliance pathway for RED cybersecurity requirements. The work you invest in EN 18031 documentation - security asset inventories, compliance tables, decision tree assessments, test plans - directly builds toward CRA compliance as well. Every section completed, every decision tree navigated, every test plan verdict recorded is a step closer to both regulatory frameworks.
The manufacturers who start preparing now will have a significant advantage: smoother market access, lower audit risk, and a compliance foundation that adapts as new regulations and standards emerge. Those who wait face compressed timelines, rushed documentation, and the risk of non-compliance when it matters most.
Getting Started with RedComply
RedComply is a cybersecurity compliance automation platform purpose-built for EN 18031 and the RED Directive. It transforms the complex, document-heavy process of preparing RED cybersecurity technical documentation into a guided, structured, AI-assisted workflow.
Here is how RedComply helps you prepare:
Create a project and select which EN 18031 parts apply to your product (1, 2, 3, or any combination)
Identify security assets with structured tables that enforce the mandatory asset-to-function mapping
Complete compliance sections using guided tables, decision trees, and an AI assistant that understands EN 18031
Generate test plans with auto-calculated verdicts across all three assessment tiers
Export your Declaration of Conformity as a structured PDF ready for regulatory review
Maintain compliance by updating documentation as your product evolves - without starting from scratch
The built-in AI assistant can search the EN 18031 standard, answer context-specific questions, suggest appropriate responses, and help you navigate complex decision trees - all within the same interface where you manage your compliance data.
Visit redcomply.com to start preparing for EU cybersecurity compliance today.