EN 18031 vs. the EU Cyber Resilience Act: How They Relate
EN 18031 and the EU Cyber Resilience Act (CRA) are not competing rulebooks - they are layered. EN 18031 is the harmonised standard that proves cybersecurity for radio equipment under the RED Directive today; the CRA is the EU-wide regulation for all products with digital elements that becomes fully applicable in 2027. This guide explains exactly how the two interact, where they overlap, and what manufacturers must do under each.
May 3, 2026
Key Takeaways
EN 18031 and the EU Cyber Resilience Act (CRA) are two cornerstones of the EU's evolving cybersecurity regime, but they sit at different levels: EN 18031 is a harmonised technical standard used to demonstrate compliance with the cybersecurity articles of the Radio Equipment Directive (RED), while the CRA is a binding horizontal regulation covering virtually every product with digital elements placed on the EU market.
EN 18031 already applies: Its three parts (EN 18031-1/-2/-3) became mandatory for radio equipment under Delegated Regulation (EU) 2022/30 on 1 August 2025.
The CRA applies later, but covers more: Regulation (EU) 2024/2847 entered into force on 10 December 2024; vulnerability and incident reporting obligations apply from 11 September 2026, and the main obligations apply from 11 December 2027.
They are complementary, not duplicative: Under CRA Article 2(4), radio equipment that is already subject to RED's cybersecurity essential requirements (i.e. EN 18031) is carved out of the corresponding CRA requirements - but only for the requirements that overlap.
The CRA goes beyond EN 18031 for everyone: Vulnerability handling, free security updates over a defined support period, an SBOM, and mandatory incident reporting to ENISA are CRA obligations that EN 18031 does not impose.
Most connected device manufacturers will face both: A wireless smart product placed on the EU market will typically rely on EN 18031 for its RED conformity and meet the CRA's lifecycle, transparency, and reporting obligations.
The Short Answer: How EN 18031 and the CRA Relate
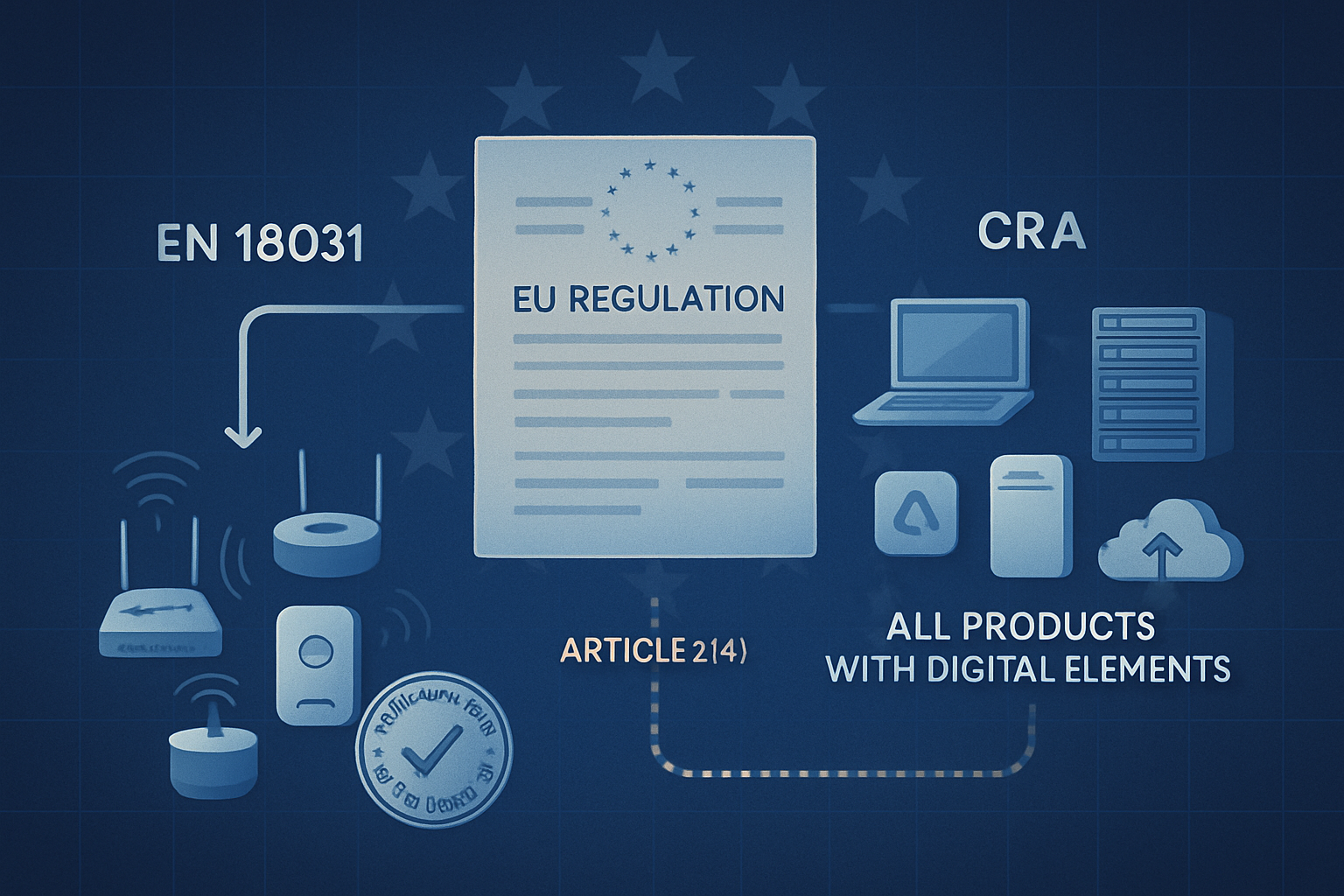
EN 18031 is a harmonised European standard that gives manufacturers a presumption of conformity with the cybersecurity essential requirements of the Radio Equipment Directive - Articles 3.3(d) (network protection), 3.3(e) (privacy and personal data), and 3.3(f) (fraud prevention). The EU Cyber Resilience Act is a horizontal regulation that imposes cybersecurity obligations on all products with digital elements placed on the EU market - connected and non-connected, hardware and software.
The two frameworks are deliberately layered. CRA Article 2(4) carves out radio equipment that is already subject to the RED cybersecurity essential requirements, so manufacturers do not need to comply with the same requirement under both regimes. In practice, this means EN 18031 remains the technical execution layer for the cybersecurity of radio equipment, while the CRA adds obligations that the RED never covered - most notably ongoing vulnerability handling, security update support, SBOM disclosure, and incident reporting to ENISA.
Put differently: EN 18031 tells you how to prove the cybersecurity of a wireless product today; the CRA tells you what additional ongoing obligations you carry once that product is on the market - and what cybersecurity floor every other digital product must meet from 2027.
What Is EN 18031?
EN 18031 is a three-part harmonised European standard published by CEN-CENELEC (JTC 13) to support the cybersecurity essential requirements activated by Delegated Regulation (EU) 2022/30 under the Radio Equipment Directive 2014/53/EU. It became a harmonised standard for the RED on 30 January 2025 and compliance with it became mandatory for radio equipment placed on the EU market on 1 August 2025.
The three parts of EN 18031
EN 18031-1: Common security requirements for internet-connected radio equipment - addresses RED Article 3.3(d) (network protection).
EN 18031-2: Requirements for radio equipment that processes virtual money, monetary value, or personal data - addresses RED Article 3.3(e) (privacy/personal data).
EN 18031-3: Requirements for radio equipment that processes virtual money or monetary value - addresses RED Article 3.3(f) (fraud prevention).
Following EN 18031 is the most efficient compliance path for radio equipment because it grants a presumption of conformity with the corresponding RED articles. When a manufacturer applies the standard fully and triggers no restrictions, conformity can be self-declared via Module A (internal production control) - no notified body required. If any restriction is triggered (for example, the EN 18031-1/-2 clauses on skippable passwords), Module B+C with a notified body is required instead.
For a deeper dive into the RED cybersecurity requirements themselves, see our RED cybersecurity overview and the essential cybersecurity standards for IoT.
What Is the EU Cyber Resilience Act (CRA)?
The Cyber Resilience Act, formally Regulation (EU) 2024/2847, is the EU's first horizontal cybersecurity law for products with digital elements (PDEs). A product with digital elements is broadly defined as any software or hardware product, plus its remote data-processing solutions, whose intended or reasonably foreseeable use includes a logical or physical data connection to a device or network.
Key dates in the CRA timeline
10 December 2024: CRA entered into force.
11 June 2026: Conformity assessment provisions for notified bodies start applying.
11 September 2026: Manufacturer vulnerability and incident reporting obligations to ENISA start applying.
11 December 2027: Main obligations become applicable to all in-scope products placed on the EU market.
What the CRA requires
Essential cybersecurity requirements in Annex I (e.g. secure-by-default configuration, protection of confidentiality and integrity, minimisation of attack surface, secure update mechanisms).
Vulnerability handling processes (Annex I, Part II) - including coordinated disclosure, ongoing testing, and a Software Bill of Materials (SBOM).
Free security updates for the longer of the product's expected lifetime or at least five years (with explicit guidance on the support period).
Incident and vulnerability reporting: actively exploited vulnerabilities and severe incidents must be notified to ENISA via an early warning within 24 hours, an incident notification within 72 hours, and a final report within 14 days.
Conformity assessment: self-assessment for default-class products, third-party assessment for important and critical products (Annex III/IV).
CE marking as the visible proof of compliance, plus technical documentation retained for at least 10 years.
Penalties under the CRA are significant: up to €15 million or 2.5% of global annual turnover, whichever is higher, for breaches of the essential cybersecurity requirements.
Side-by-Side Comparison: EN 18031 vs. the CRA
The clearest way to understand the relationship is to compare the two frameworks across the dimensions that matter to a manufacturer - legal nature, scope, timing, technical depth, lifecycle obligations, and conformity assessment route.
| Dimension | EN 18031 | Cyber Resilience Act |
|---|---|---|
Legal nature | Harmonised European technical standard (voluntary, but grants presumption of conformity) | Binding EU regulation, directly applicable in all Member States |
Underlying instrument | Supports RED Directive 2014/53/EU + Delegated Regulation (EU) 2022/30 | Regulation (EU) 2024/2847 (standalone horizontal law) |
Scope | Internet-connected radio equipment placed on the EU market | All products with digital elements (hardware + software + remote data-processing solutions) |
Mandatory since / from | 1 August 2025 | 11 September 2026 (reporting); 11 December 2027 (full obligations) |
Conformity assessment | Module A self-assessment via EN 18031, or Module B+C with notified body if restrictions are triggered | Self-assessment for default class; third-party assessment for important (Annex III) and critical (Annex IV) products |
Technical depth | Detailed clauses, decision trees, assessment units per asset category | High-level essential requirements (Annex I) + Annex I Part II vulnerability handling processes |
Asset categories addressed | Network, security, privacy, financial assets - explicitly mapped to RED 3.3(d)/(e)/(f) | Generic cybersecurity properties - implementer must derive technical controls |
Vulnerability handling | Not directly addressed | Mandatory: coordinated disclosure, ongoing testing, SBOM, fix delivery |
Security update obligations | Update mechanism must be secure (clause level) but no minimum support period | Free security updates for expected product lifetime, typically at least 5 years |
Incident / vulnerability reporting | Not required by the standard itself | Mandatory reporting to ENISA: 24h early warning, 72h notification, 14-day final report |
Visible mark | CE marking via RED conformity | CE marking via CRA conformity |
Penalties | Set by Member States under RED national transposition | Up to €15M or 2.5% of global turnover |
Where They Overlap and Where the CRA Goes Further
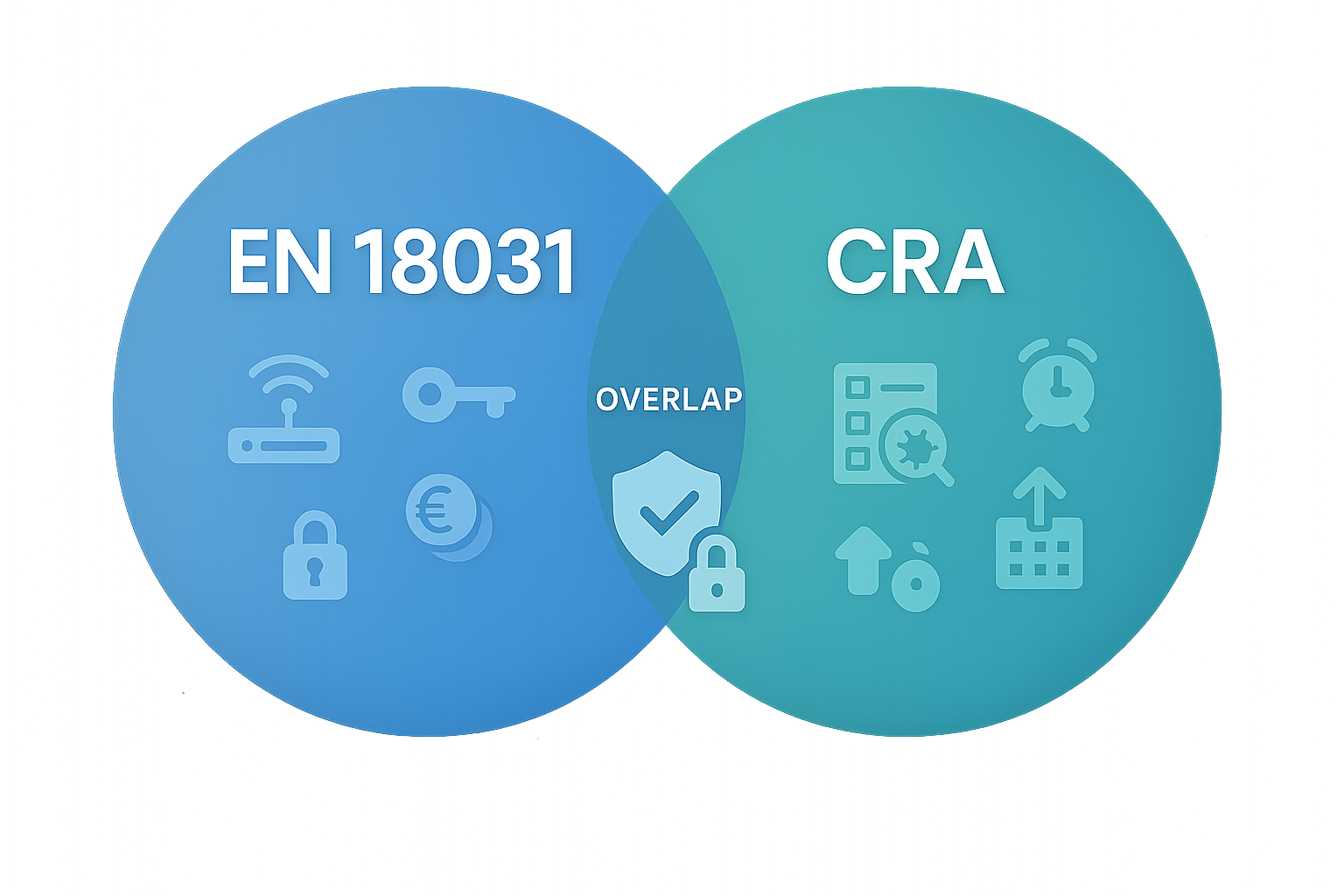
Many of the essential cybersecurity requirements in CRA Annex I overlap with what EN 18031 already asks of radio equipment - confidentiality, integrity, secure configuration, minimisation of attack surface, secure communications, secure software updates, access control, and protection against unauthorised access. This is why CRA Article 2(4) exists: when a radio equipment product is subject to the RED cybersecurity essential requirements (and therefore to EN 18031 in practice), the corresponding CRA requirements do not apply twice.
What overlaps (CRA carve-out for radio equipment)
Protection against unauthorised access and authentication mechanisms
Confidentiality and integrity of stored, transmitted and processed data
Minimisation of attack surface and secure-by-default configuration
Secure communication channels and cryptographic baseline
Secure software update mechanisms (the technical side of the update)
Where the CRA adds genuinely new obligations
Vulnerability handling lifecycle: a documented coordinated disclosure policy, ongoing internal testing, and a clear process for triaging and remediating reported vulnerabilities.
Software Bill of Materials (SBOM): a machine-readable inventory of components and dependencies for each product version, kept up to date.
Defined support period: free security updates for the expected product lifetime, with explicit guidance pointing to a minimum of five years in most cases.
Incident reporting to ENISA via the single reporting platform: 24h early warning, 72h incident notification, 14-day final report - applicable from 11 September 2026.
Conformity assessment for important and critical products: third-party assessment is required for products in Annex III (important) and Annex IV (critical), regardless of whether EN 18031 is otherwise applied.
Distributor and importer obligations: the CRA places explicit duties on the wider supply chain, not only the manufacturer.
The practical consequence is that manufacturers of radio equipment cannot treat EN 18031 as the end of their cybersecurity obligations. The standard handles the technical conformity layer; the CRA layers ongoing process and transparency obligations on top. Vulnerability disclosure programmes, support periods, and incident reporting workflows are not optional under the CRA.
For practical guidance on documenting vulnerabilities under either regime, see our vulnerability management guide.
Which Framework Applies to Your Product?
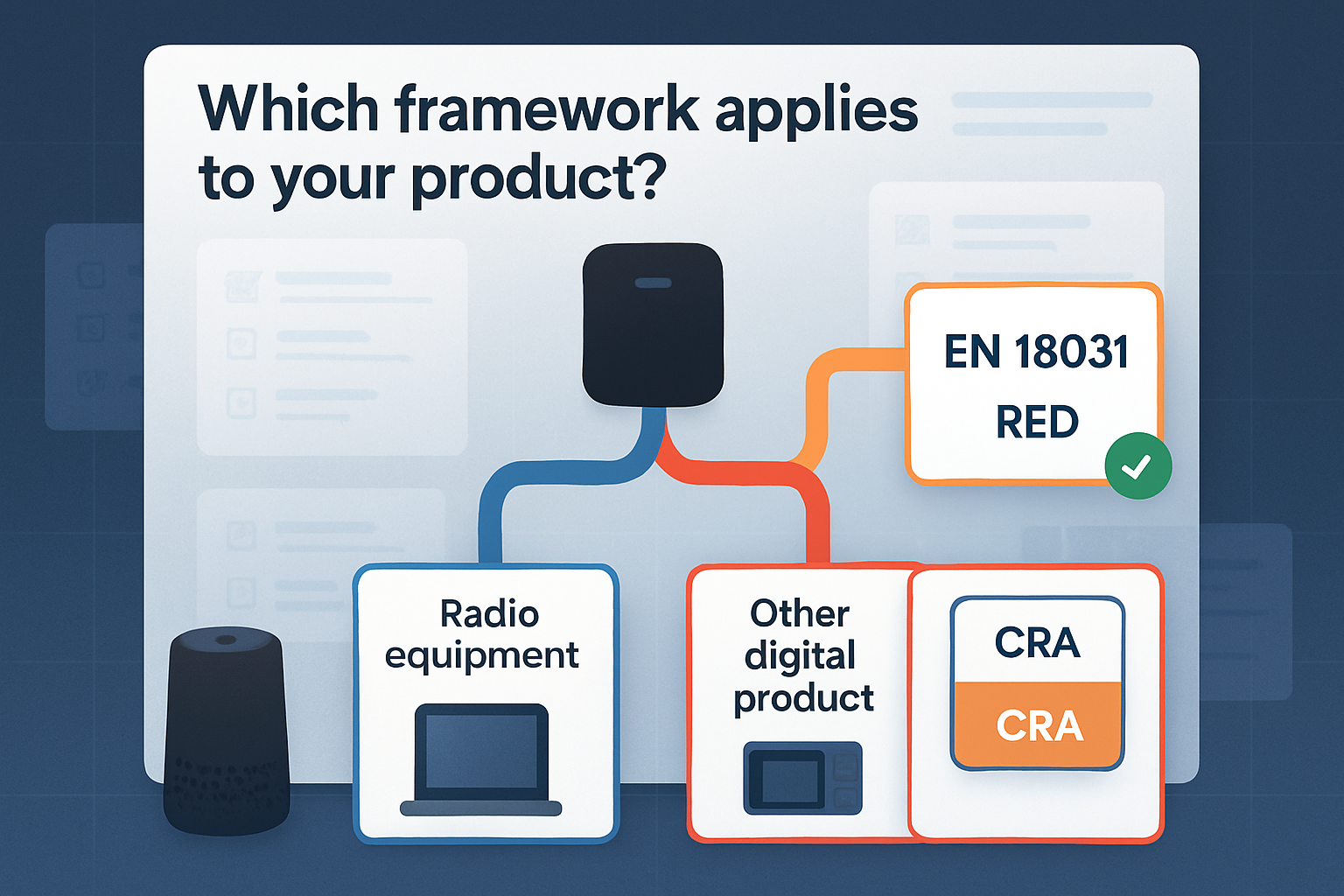
Most product-security teams confronted with both frameworks ask the same question: "do I need to comply with EN 18031, the CRA, or both?" The decision usually comes down to two questions about the product.
Is the product radio equipment in the sense of RED 2014/53/EU? That is, does it intentionally emit or receive radio waves for communication or radiodetermination? If yes, RED applies and EN 18031 is the practical compliance route.
*Does the product fall within the CRA's definition of a product with digital elements?* That is, software or hardware (plus remote data-processing solutions) whose use includes a data connection to a device or network. If yes, CRA obligations apply from 2027 (and reporting from 2026).
Three common scenarios
| Product profile | RED + EN 18031 | CRA | What you must do |
|---|---|---|---|
Wireless smart product (e.g. Wi-Fi camera, smart speaker, IoT gateway) | Yes | Yes (with Article 2(4) carve-out for overlapping requirements) | Apply EN 18031 for RED conformity now; layer CRA vulnerability handling, SBOM, support period, and incident reporting from 2026/2027 |
Non-radio digital product (e.g. desktop software, wired industrial controller, server appliance) | No | Yes | Direct CRA compliance: meet Annex I requirements, run vulnerability handling, prepare for incident reporting |
Component or development tool (e.g. firmware library, OS image, MCU module) | Possibly, depending on integration | Yes (component obligations) | Document component cybersecurity, support integrators with SBOM, and meet CRA's component-level expectations |
The biggest miscalculation we see is manufacturers of wireless devices assuming that achieving EN 18031 conformity is enough. It is not - at least not after 2026. EN 18031 closes the RED loop; the CRA adds an entirely separate set of lifecycle obligations on top.
For a broader view of how to prepare for these regulations together, see our companion guide on preparing for new EU cybersecurity regulations.
Frequently Asked Questions
Does the CRA replace EN 18031?
No. The CRA does not replace EN 18031 or the RED. Under CRA Article 2(4), radio equipment that is subject to RED's cybersecurity essential requirements (covered by EN 18031) is carved out of the overlapping CRA requirements - but it is still subject to CRA obligations that go beyond the RED, such as vulnerability handling, support periods, SBOM, and incident reporting to ENISA.
If my product complies with EN 18031, am I CRA-compliant?
Not automatically. EN 18031 covers the technical cybersecurity floor for radio equipment under RED, which overlaps significantly with CRA Annex I. However, CRA-specific obligations - vulnerability handling lifecycle, defined security update support period, SBOM, and mandatory ENISA reporting - are not part of EN 18031 and must be implemented separately. Plan for both layers if your product is wireless and digital.
When does the Cyber Resilience Act become mandatory?
The CRA entered into force on 10 December 2024. Manufacturer vulnerability and incident reporting obligations apply from 11 September 2026, and the main obligations (essential cybersecurity requirements, technical documentation, CE marking) apply from 11 December 2027. EN 18031 has been mandatory under the RED since 1 August 2025.
Will EN 18031 also support CRA conformity in the future?
It is widely expected that EN 18031 - or a successor harmonised standard mapped to CRA Annex I - will play a central role in the CRA's harmonised standards landscape. ENISA and CEN-CENELEC are working on mapping the CRA's essential requirements to existing standards, and EN 18031 is a strong candidate for the cybersecurity floor of connected products. Manufacturers should still treat EN 18031 and the CRA as distinct compliance tracks until harmonised standards under the CRA are formally published.
Do I need a notified body for EN 18031 or for the CRA?
Under EN 18031 + RED, a notified body is generally not required if you apply the standard fully and trigger no restrictions - Module A self-assessment is allowed. Under the CRA, third-party conformity assessment by a notified body is required for products classified as important (Annex III) or critical (Annex IV); other products can self-assess against Annex I.
Conclusion: Complementary, Not Competing
EN 18031 and the EU Cyber Resilience Act are complementary frameworks that together define how the EU regulates the cybersecurity of connected products. EN 18031 is the technical standard you reach for today to demonstrate RED cybersecurity conformity for radio equipment. The CRA is the broader, slower-moving horizontal regulation that adds lifecycle, transparency, and reporting obligations that no harmonised standard previously imposed.
EN 18031 = harmonised standard, mandatory now under RED for radio equipment, focused on technical conformity.
Cyber Resilience Act = horizontal regulation, mandatory from 2026/2027, focused on essential requirements and lifecycle obligations.
CRA Article 2(4) carves radio equipment out of duplicated requirements, not out of the CRA entirely.
Vulnerability handling, SBOM, support period, and ENISA reporting are CRA-only obligations - plan for them now even if you already follow EN 18031.
Most connected-device manufacturers will need to comply with both in parallel.
The right mental model is layers: EN 18031 is the technical floor for radio equipment under RED; the CRA is the horizontal regulatory ceiling that defines the EU's expectations for every digital product on the market. Manufacturers who design their compliance programme to meet both - and who treat compliance as a continuous workflow - will be in the strongest position when market surveillance and ENISA reporting begin in earnest.
How RedComply Helps You Stay Ahead of EN 18031 (and Get Ready for the CRA)
RedComply is purpose-built for EN 18031 and the RED cybersecurity regime. Today it automates the full EN 18031 workflow end-to-end; dedicated Cyber Resilience Act support is on our roadmap and coming soon. Rather than juggling spreadsheets, decision trees on paper, and ad-hoc PDFs, you get a single workspace where your RED compliance work also lays the groundwork for the lifecycle obligations the CRA will introduce.
Here is what RedComply automates for EN 18031 today:
EN 18031-aligned templates for all three parts (-1, -2, -3), with section, table, and decision tree coverage mapped to RED Articles 3.3(d), 3.3(e), and 3.3(f).
Asset inventories (security, network, privacy, financial) that capture every relevant asset once and reuse it across the standard.
Decision trees that automate PASS/FAIL/NOT_ASSESSED outcomes for every EN 18031 requirement and produce auditable evaluator notes.
Test plans with auto-calculated verdicts for conceptual, completeness, and sufficiency assessments - ready for self-declaration via Module A.
One-click Declaration of Conformity (DoC) generation that compiles your current compliance state into a structured PDF, including equipment identification rendered vertically as required.
AI assistant trained on EN 18031 that searches the standard, your uploaded technical documentation, and your project's compliance tables - and can directly help fill in tables and justifications.
On the CRA side, dedicated automation is coming soon. The structured documentation, asset inventories, and evidence trails you build today in RedComply for EN 18031 are exactly the foundation we will extend to support CRA-specific deliverables - vulnerability handling policies, SBOM references, support period statements, and incident reporting workflows - as that functionality ships.
Stop tracking EN 18031 in disconnected spreadsheets and get ahead of the CRA at the same time. Visit redcomply.com to see how a single structured workspace automates your EN 18031 compliance today and is being built to carry that work into the full CRA timeline in 2026 and 2027.